Aerospace engineers sometimes compute the trajectories of projectiles like rockets. A related problem deals with the trajectory of a thrown ball. The trajectory of a ball is defined by the
Find the appropriate initial angle
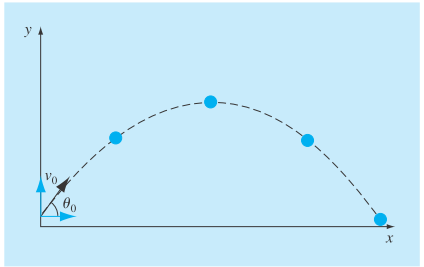
FIGURE P8.37
Want to see the full answer?
Check out a sample textbook solution
Chapter 8 Solutions
Numerical Methods for Engineers
Additional Math Textbook Solutions
College Algebra (7th Edition)
University Calculus
Introductory Statistics
Finite Mathematics for Business, Economics, Life Sciences and Social Sciences
Mathematics for the Trades: A Guided Approach (11th Edition) (What's New in Trade Math)
Elementary Statistics (13th Edition)
- Using Karnaugh maps and Gray coding, reduce the following circuit represented as a table and write the final circuit in simplest form (first in terms of number of gates then in terms of fan-in of those gates). HINT: Pay closeattention to both the 1’s and the 0’s of the function.arrow_forwardRecall the RSA encryption/decryption system. The following questions are based on RSA. Suppose n (=15) is the product of the two prime numbers 3 and 5.1. Find an encryption key e for for the pair (e, n)2. Find a decryption key d for for the pair (d, n)3. Given the plaintext message x = 3, find the ciphertext y = x^(e) (where x^e is the message x encoded with encryption key e)4. Given the ciphertext message y (which you found in previous part), Show that the original message x = 3 can be recovered using (d, n)arrow_forwardTheorem 1: A number n ∈ N is divisible by 3 if and only if when n is writtenin base 10 the sum of its digits is divisible by 3. As an example, 132 is divisible by 3 and 1 + 3 + 2 is divisible by 3.1. Prove Theorem 1 2. Using Theorem 1 construct an NFA over the alphabet Σ = {0, 1, 2, 3, 4, 5, 6, 7, 8, 9}which recognizes the language {w ∈ Σ^(∗)| w = 3k, k ∈ N}.arrow_forward
- Recall the RSA encryption/decryption system. The following questions are based on RSA. Suppose n (=15) is the product of the two prime numbers 3 and 5.1. Find an encryption key e for for the pair (e, n)2. Find a decryption key d for for the pair (d, n)3. Given the plaintext message x = 3, find the ciphertext y = x^(e) (where x^e is the message x encoded with encryption key e)4. Given the ciphertext message y (which you found in previous part), Show that the original message x = 3 can be recovered using (d, n)arrow_forwardFind the sum of products expansion of the function F(x, y, z) = ¯x · y + x · z in two ways: (i) using a table; and (ii) using Boolean identities.arrow_forwardGive both a machine-level description (i.e., step-by-step description in words) and a state-diagram for a Turing machine that accepts all words over the alphabet {a, b} where the number of a’s is greater than or equal to the number of b’s.arrow_forward
- Compute (7^ (25)) mod 11 via the algorithm for modular exponentiation.arrow_forwardProve that the sum of the degrees in the interior angles of any convex polygon with n ≥ 3 sides is (n − 2) · 180. For the base case, you must prove that a triangle has angles summing to 180 degrees. You are permitted to use thefact when two parallel lines are cut by a transversal that corresponding angles are equal.arrow_forwardAnswer the following questions about rational and irrational numbers.1. Prove or disprove: If a and b are rational numbers then a^b is rational.2. Prove or disprove: If a and b are irrational numbers then a^b is irrational.arrow_forward
 Trigonometry (MindTap Course List)TrigonometryISBN:9781337278461Author:Ron LarsonPublisher:Cengage LearningAlgebra & Trigonometry with Analytic GeometryAlgebraISBN:9781133382119Author:SwokowskiPublisher:Cengage
Trigonometry (MindTap Course List)TrigonometryISBN:9781337278461Author:Ron LarsonPublisher:Cengage LearningAlgebra & Trigonometry with Analytic GeometryAlgebraISBN:9781133382119Author:SwokowskiPublisher:Cengage Trigonometry (MindTap Course List)TrigonometryISBN:9781305652224Author:Charles P. McKeague, Mark D. TurnerPublisher:Cengage Learning
Trigonometry (MindTap Course List)TrigonometryISBN:9781305652224Author:Charles P. McKeague, Mark D. TurnerPublisher:Cengage Learning Elements Of Modern AlgebraAlgebraISBN:9781285463230Author:Gilbert, Linda, JimmiePublisher:Cengage Learning,
Elements Of Modern AlgebraAlgebraISBN:9781285463230Author:Gilbert, Linda, JimmiePublisher:Cengage Learning,