Problems 7 through 10 deal with the RC circuit in Fig. 3.7.8, containing a resistor (R ohms), a capacitor (C farads), a switch, a source of emf, but no inductor Substitution of
for the charge
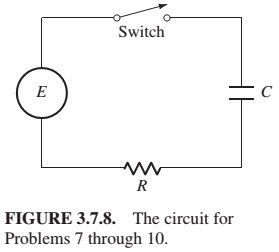
(a) Find the charge Q (t ) and current I (t ) in the RC circuit if
Trending nowThis is a popular solution!

Chapter 3 Solutions
Differential Equations: Computing and Modeling (5th Edition), Edwards, Penney & Calvis
Additional Engineering Textbook Solutions
Mechanics of Materials (10th Edition)
Starting Out with C++ from Control Structures to Objects (9th Edition)
Modern Database Management
Java: An Introduction to Problem Solving and Programming (8th Edition)
Starting Out with Programming Logic and Design (5th Edition) (What's New in Computer Science)
Java How to Program, Early Objects (11th Edition) (Deitel: How to Program)
- using the fill function in python fill elements of a list with a given value def fill(data, value) :arrow_forwardComplete the following program that creates a duplicate version of a list but with the elements stored in reverse order from the original. origValues = [1, 5, 65, 30, 200, 46, 48, 5, 14, 30] newValues = []arrow_forwardUsing python code Find maximum value of a list: values = [2, 45, 3, 25, 6, 8, 5, 100, 104] Then, remove that maximum value from the listarrow_forward
- How to modify the code below so that it prints all possitive values in a list that is separated by commas? values = [1, -2, 3, 4] for i in range(len(values)) : if i > 0 : print(" | ", end="") print(values[i], end="")print()arrow_forwardusiing python remove all negative values from a list of values values = [34, -8, -5, 4, 6, 7]arrow_forwardUsing python, remove highes and lowest score and then sum the remaining 6 scores: scores = [1.4, 5.5, 4.7, 2.0, 6.3, 7.5, 2.6, 5.3, 8.1] totalScore= print("Score = %5.2f" % totalScorearrow_forward
- What are quantitative and qualitative data? Describe an example of a use case and visual representation for qualitative data and one for quantitative data from your organization.arrow_forward1. Checksum. Assuming the following IP header lacking checksum: 01000101.00000000.11000011.00101010. 00000000.00000000.00000000.00000000. 10000000.00000000.00000000.00000000. <- checksum 01100011.11011001.00000000.00000001. 10000000.00000000.00000000.00000010 Compute its checksumarrow_forwardI would like to know the features of BranchCache, Metadata, and LPR Port Monitorarrow_forward
- Please answer the JAVA OOP questions below: How do arrays of objects differ from arrays of primitive types? Why and when would you use an array of objects? What are the different ways to initialize an array of objects? What is a static variable in Java? How does its scope differ from instance variables? When should you use static variables? Provide examples where static variables are beneficial over instance variables. What is the difference between static and non-static methods in the Data Definition Class? What are the benefits of using static methods?arrow_forwardAssume you are a loyal member of Costco. You have been expecting your membership reward from the company, and you just received a text message on your mobile phone. The message appears to be from Costco: Costco - Your 3% return is ready: costco.wholesaledividend.com Before clicking the link in the message, you consider whether this is genuinely from Costco or a phishing attack on you. How can you tell? If it is a phishing attack, what mechanism was most likely used to send the message to you? What actions can you take if you are not sure whether it is a genuine message from Costco? What actions can you take if you are sure this is a phishing attack?arrow_forwardRSA and Diffie-Hellman are important algorithms in public-key cryptography. What are the differences between the two? Assume you intercept the ciphertext C = 105 sent to a user whose public key is e = 7, n = 403. Explain in detail how you will find the private key of the user and crack the ciphertext. What is the plaintext M?arrow_forward
 C++ for Engineers and ScientistsComputer ScienceISBN:9781133187844Author:Bronson, Gary J.Publisher:Course Technology Ptr
C++ for Engineers and ScientistsComputer ScienceISBN:9781133187844Author:Bronson, Gary J.Publisher:Course Technology Ptr Operations Research : Applications and AlgorithmsComputer ScienceISBN:9780534380588Author:Wayne L. WinstonPublisher:Brooks Cole
Operations Research : Applications and AlgorithmsComputer ScienceISBN:9780534380588Author:Wayne L. WinstonPublisher:Brooks Cole Systems ArchitectureComputer ScienceISBN:9781305080195Author:Stephen D. BurdPublisher:Cengage Learning
Systems ArchitectureComputer ScienceISBN:9781305080195Author:Stephen D. BurdPublisher:Cengage Learning Principles of Information Systems (MindTap Course...Computer ScienceISBN:9781285867168Author:Ralph Stair, George ReynoldsPublisher:Cengage Learning
Principles of Information Systems (MindTap Course...Computer ScienceISBN:9781285867168Author:Ralph Stair, George ReynoldsPublisher:Cengage Learning



