
Java: An Introduction to Problem Solving and Programming (8th Edition)
8th Edition
ISBN: 9780134462035
Author: Walter Savitch
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Textbook Question
Chapter 3.3, Problem 18STQ
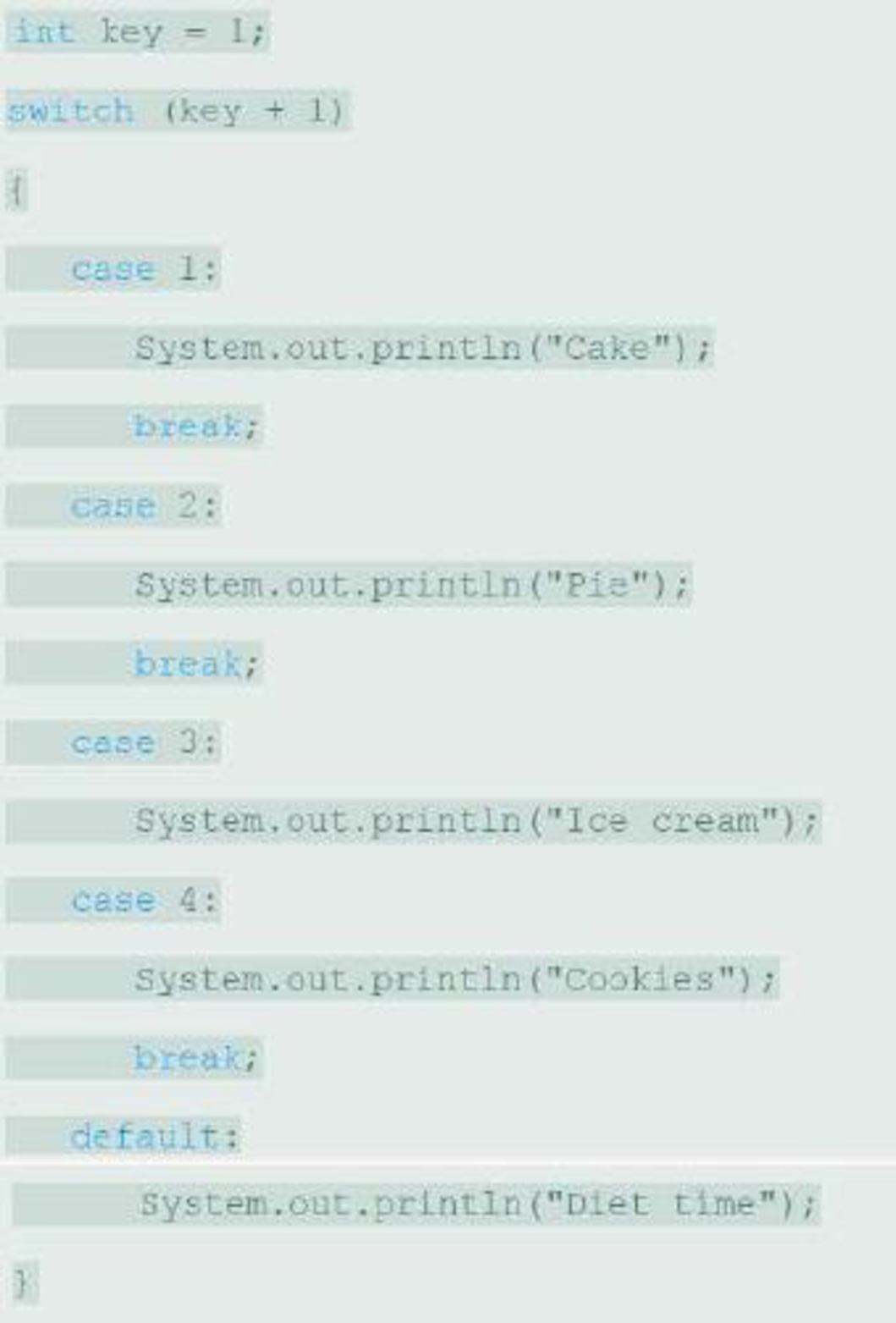
What output is produced by the following code?
Expert Solution & Answer
Want to see the full answer?
Check out a sample textbook solution
Students have asked these similar questions
Dijkstra's Algorithm (part 1). Consider the network shown below, and Dijkstra’s link-state algorithm. Here, we are interested in computing the least cost path from node E (note: the start node here is E) to all other nodes using Dijkstra's algorithm. Using the algorithm statement used in the textbook and its visual representation, complete the "Step 0" row in the table below showing the link state algorithm’s execution by matching the table entries (i), (ii), (iii), and (iv) with their values. Write down your final [correct] answer, as you‘ll need it for the next question.
4. |z + 5 - 5i| = 7
14.
dz,
C: |z❘
C: |z❘ = 0.6
ze² - 2iz
H
Chapter 3 Solutions
Java: An Introduction to Problem Solving and Programming (8th Edition)
Ch. 3.1 - Suppose goals is a variable of type int. Write an...Ch. 3.1 - Suppose goals and errors are variables of type...Ch. 3.1 - Suppose salary and deductions are variables of...Ch. 3.1 - Suppose speed and visibility are variables of type...Ch. 3.1 - Suppose salary and bonus are variables of type...Ch. 3.1 - Assume that nextWord is a string variable that has...Ch. 3.1 - Prob. 7STQCh. 3.1 - What output is produced by the following code? int...Ch. 3.1 - Suppose you change the code in the previous...Ch. 3.1 - What output is produced by the following code? int...
Ch. 3.2 - Suppose number is a variable of type int that has...Ch. 3.2 - What output is produced by the following...Ch. 3.2 - What output is produced by the following...Ch. 3.2 - What output is produced by the following...Ch. 3.3 - What output is produced by the following code?Ch. 3.3 - Suppose you change the code in the previous...Ch. 3.3 - What output is produced by the following code?Ch. 3.3 - What output is produced by the following code?Ch. 3.3 - Suppose you change the first line of the code in...Ch. 3.3 - Prob. 20STQCh. 3.4 - Suppose you change the order of the drawing...Ch. 3.4 - Prob. 22STQCh. 3.4 - Write code for a JOptionPane dialog that will ask...Ch. 3 - Write a fragment of code that will test whether an...Ch. 3 - Write a fragment of code that will change the...Ch. 3 - Suppose you are writing a program that asks the...Ch. 3 - Prob. 4ECh. 3 - Consider the following fragment of code: What is...Ch. 3 - We would like to assess a service charge for...Ch. 3 - What is the value of each of the following boolean...Ch. 3 - The following code fragment will not compile. Why?...Ch. 3 - Prob. 9ECh. 3 - Consider the boolean expression (2 5) (x 100))....Ch. 3 - Write a switch statement to convert a letter grade...Ch. 3 - Consider the previous question, but include + or ...Ch. 3 - Imagine a program that displays a menu of five...Ch. 3 - Repeat the previous exercise, but define an...Ch. 3 - Repeat Exercise 13, but use a multibranch if-else...Ch. 3 - Given that the int variable temp contains a...Ch. 3 - Write Java statements that create a yes-or-no...Ch. 3 - A number x is divisible by y if the remainder...Ch. 3 - Write a program to read in three nonnegative...Ch. 3 - Write a program that reads three strings from the...Ch. 3 - Write a program that reads a one-line sentence as...Ch. 3 - Write a program that allows the user to convert a...Ch. 3 - Write a program that inputs an integer. If the...Ch. 3 - Prob. 7PCh. 3 - Repeat Programming Project 5 of Chapter 2, but...Ch. 3 - Repeat any of the previous Practice Programs using...Ch. 3 - Suppose that we are working for an online service...Ch. 3 - Write a program that reads a string from the...Ch. 3 - Repeat the calorie-counting program described in...Ch. 3 - Repeat Programming Project 5 but in addition ask...Ch. 3 - Repeat Programming Project 11 in Chapter 2, but if...Ch. 3 - Write a program to play the rock-paper-scissor...Ch. 3 - Prob. 9PPCh. 3 - Repeat Programming Project 8 in Chapter 1, but add...Ch. 3 - Write a program that inputs two strings that...
Additional Engineering Textbook Solutions
Find more solutions based on key concepts
The base class named in the following line of code is _____. class Pet : public Dog
Starting Out with C++: Early Objects (9th Edition)
Declare method sphereVolume to calculate and return the volume of the sphere. Use the following statement to ca...
Java How to Program, Early Objects (11th Edition) (Deitel: How to Program)
In Exercises 41 through 46, identify the errors. Dim9WAsDouble9W=2*9WIstoutput.Items.Add(9W)
Introduction To Programming Using Visual Basic (11th Edition)
Why is the study of database technology important?
Database Concepts (8th Edition)
Corporate Sales A corporation has six divisions, each responsible for sales to different geographic locations. ...
Starting Out with C++ from Control Structures to Objects (9th Edition)
2-1 List the five types of measurements that form the
basis of traditional ptane surveying-
Elementary Surveying: An Introduction To Geomatics (15th Edition)
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage Learning
C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage Learning Microsoft Visual C#Computer ScienceISBN:9781337102100Author:Joyce, Farrell.Publisher:Cengage Learning,
Microsoft Visual C#Computer ScienceISBN:9781337102100Author:Joyce, Farrell.Publisher:Cengage Learning, EBK JAVA PROGRAMMINGComputer ScienceISBN:9781337671385Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT
EBK JAVA PROGRAMMINGComputer ScienceISBN:9781337671385Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT C++ for Engineers and ScientistsComputer ScienceISBN:9781133187844Author:Bronson, Gary J.Publisher:Course Technology PtrProgramming Logic & Design ComprehensiveComputer ScienceISBN:9781337669405Author:FARRELLPublisher:Cengage
C++ for Engineers and ScientistsComputer ScienceISBN:9781133187844Author:Bronson, Gary J.Publisher:Course Technology PtrProgramming Logic & Design ComprehensiveComputer ScienceISBN:9781337669405Author:FARRELLPublisher:Cengage

C++ Programming: From Problem Analysis to Program...
Computer Science
ISBN:9781337102087
Author:D. S. Malik
Publisher:Cengage Learning

Microsoft Visual C#
Computer Science
ISBN:9781337102100
Author:Joyce, Farrell.
Publisher:Cengage Learning,

EBK JAVA PROGRAMMING
Computer Science
ISBN:9781337671385
Author:FARRELL
Publisher:CENGAGE LEARNING - CONSIGNMENT

C++ for Engineers and Scientists
Computer Science
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Course Technology Ptr

Programming Logic & Design Comprehensive
Computer Science
ISBN:9781337669405
Author:FARRELL
Publisher:Cengage
C++ Programming Tutorial 36 - Intro to Loops; Author: Caleb Curry;https://www.youtube.com/watch?v=M3o7Y0juEP0;License: Standard YouTube License, CC-BY