Database Systems: Design, Implementation, & Management
12th Edition
ISBN: 9781305627482
Author: Carlos Coronel, Steven Morris
Publisher: Cengage Learning
expand_more
expand_more
format_list_bulleted
Concept explainers
Textbook Question
Chapter 3, Problem 17P
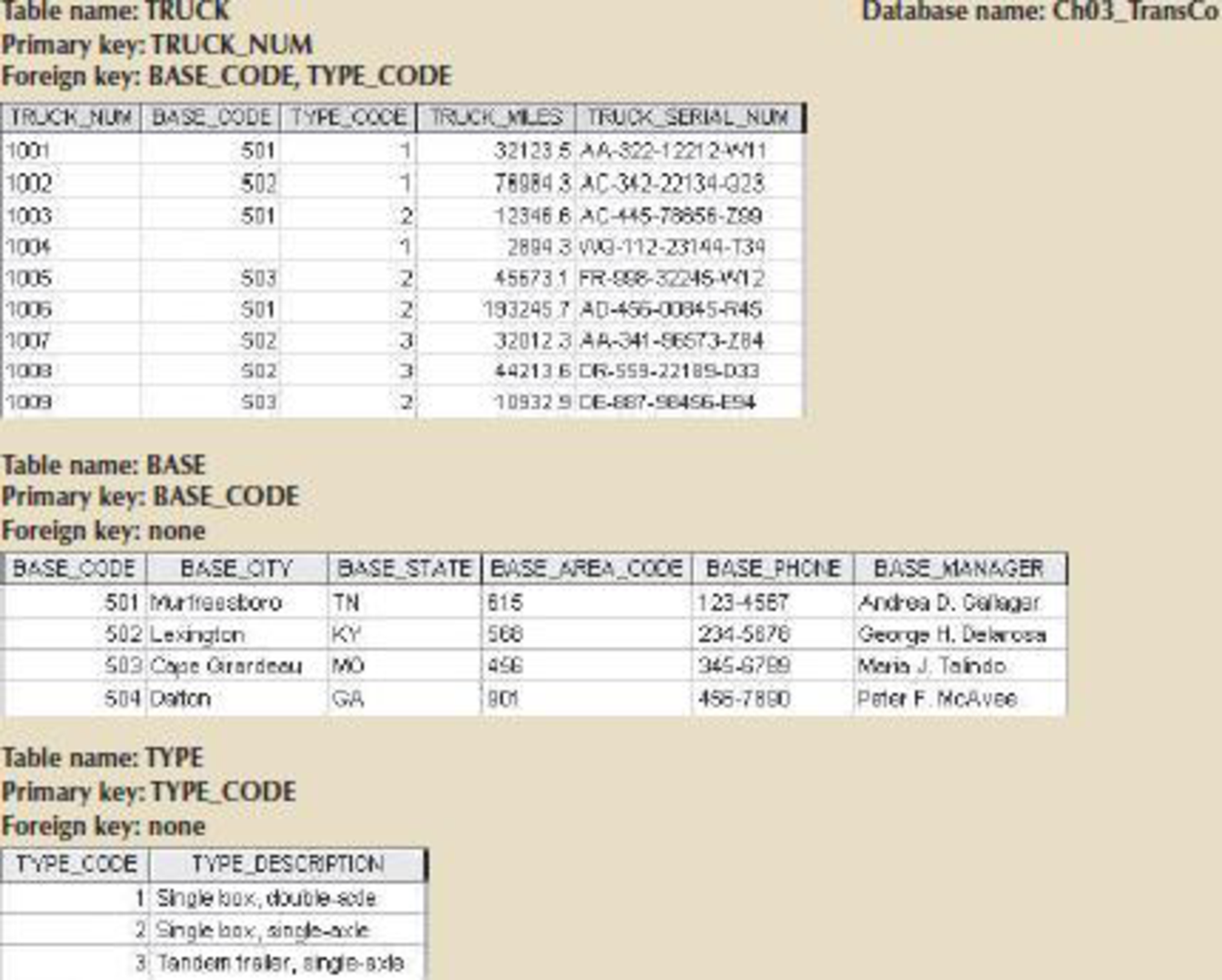
For each table, identify the primary key and the foreign key(s). If a table does not have a foreign key, write None.
FIGURE P3.17 THE CH03_TRANSCO
Expert Solution & Answer
Trending nowThis is a popular solution!

Students have asked these similar questions
Dijkstra's Algorithm (part 1). Consider the network shown below, and Dijkstra’s link-state algorithm. Here, we are interested in computing the least cost path from node E (note: the start node here is E) to all other nodes using Dijkstra's algorithm. Using the algorithm statement used in the textbook and its visual representation, complete the "Step 0" row in the table below showing the link state algorithm’s execution by matching the table entries (i), (ii), (iii), and (iv) with their values. Write down your final [correct] answer, as you‘ll need it for the next question.
4. |z + 5 - 5i| = 7
14.
dz,
C: |z❘
C: |z❘ = 0.6
ze² - 2iz
H
Chapter 3 Solutions
Database Systems: Design, Implementation, & Management
Ch. 3 - What is the difference between a database and a...Ch. 3 - Prob. 2RQCh. 3 - Prob. 3RQCh. 3 - What are the requirements that two relations must...Ch. 3 - Which relational algebra operators can be applied...Ch. 3 - Explain why the data dictionary is sometimes...Ch. 3 - A database user manually notes that The file...Ch. 3 - Prob. 8RQCh. 3 - Prob. 9RQCh. 3 - Prob. 10RQ
Ch. 3 - Prob. 11RQCh. 3 - Prob. 12RQCh. 3 - Use Figure Q3.13 to answer Questions 1317. FIGURE...Ch. 3 - Create the table that results from applying a...Ch. 3 - Write the relational algebra formula to apply an...Ch. 3 - Create the table that results from applying an...Ch. 3 - Using the tables in Figure Q3.13, create the table...Ch. 3 - Prob. 18RQCh. 3 - Prob. 19RQCh. 3 - Prob. 20RQCh. 3 - Identify and describe the components of the table...Ch. 3 - Identify the primary keys. FIGURE Q3.22 THE...Ch. 3 - Identify the foreign keys. FIGURE Q3.22 THE...Ch. 3 - Create the ERM. FIGURE Q3.22 THE CH03_THEATER...Ch. 3 - Create the relational diagram to show the...Ch. 3 - Prob. 26RQCh. 3 - What would be the conceptual view of the INDEX...Ch. 3 - Prob. 1PCh. 3 - Prob. 2PCh. 3 - Do the tables exhibit referential integrity?...Ch. 3 - Describe the type(s) of relationship(s) between...Ch. 3 - Prob. 5PCh. 3 - Prob. 6PCh. 3 - Prob. 7PCh. 3 - Prob. 8PCh. 3 - Create the relational diagram to show the...Ch. 3 - Prob. 10PCh. 3 - Prob. 11PCh. 3 - Create the relational diagram to show the...Ch. 3 - Prob. 13PCh. 3 - Do the tables exhibit referential integrity?...Ch. 3 - Prob. 15PCh. 3 - Prob. 16PCh. 3 - For each table, identify the primary key and the...Ch. 3 - Prob. 18PCh. 3 - Do the tables exhibit referential integrity?...Ch. 3 - Identify the TRUCK tables candidate key(s). FIGURE...Ch. 3 - For each table, identify a superkey and a...Ch. 3 - Prob. 22PCh. 3 - Prob. 23PCh. 3 - Prob. 24PCh. 3 - Create the ERD. (Hint: Look at the table contents....Ch. 3 - Prob. 26PCh. 3 - Prob. 27PCh. 3 - Prob. 28PCh. 3 - Create the table that would result from applying...Ch. 3 - Create the table that would result from applying...Ch. 3 - Create the table that would result from applying a...
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781305627482Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781305627482Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781285196145Author:Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos CoronelPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781285196145Author:Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos CoronelPublisher:Cengage Learning A Guide to SQLComputer ScienceISBN:9781111527273Author:Philip J. PrattPublisher:Course Technology Ptr
A Guide to SQLComputer ScienceISBN:9781111527273Author:Philip J. PrattPublisher:Course Technology Ptr Np Ms Office 365/Excel 2016 I NtermedComputer ScienceISBN:9781337508841Author:CareyPublisher:Cengage
Np Ms Office 365/Excel 2016 I NtermedComputer ScienceISBN:9781337508841Author:CareyPublisher:Cengage

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781305627482
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781285196145
Author:Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:Cengage Learning

A Guide to SQL
Computer Science
ISBN:9781111527273
Author:Philip J. Pratt
Publisher:Course Technology Ptr



Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:9781337508841
Author:Carey
Publisher:Cengage
SQL Basics for Beginners | Learn SQL | SQL Tutorial for Beginners | Edureka; Author: edureka;https://www.youtube.com/watch?v=zbMHLJ0dY4w;License: Standard YouTube License, CC-BY