Concept explainers
GROUP LEARNING
Current Events of an Unethical Type83
Step I. Prior to meeting as a group, each person should find two newspaper or magazine articles from the past several months relating to someone violating
Step 2. Summarize the key points of the articles you found.
Step 3. Meet as a group. Have each person share key points from articles with group members.
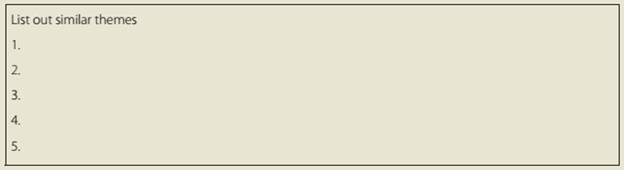
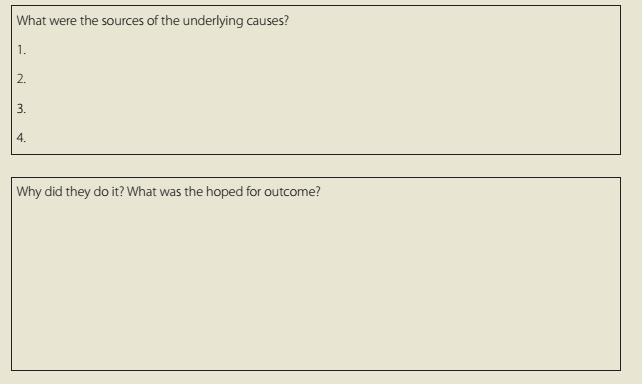
Step 4. Identify similar themes across the unethical incidents reported in the articles. What was the source or underlying cause of the unethical behavior? What was the hoped—for outcome? Was an individual or a group involved? Did the accused seem repentant or defensive? Can you identify similar conditions of any kind across incidents? Write the common themes in a list on a sheet of paper or whiteboard.
Step 5. What could you as a manager do to prevent such unethical behavior in your organization? What could you do to fix this kind of problem after it occurred in your organization?
Step 6. Report your findings to the class if asked to do so by your instructor.
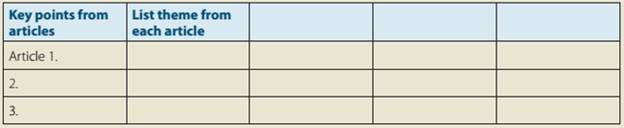
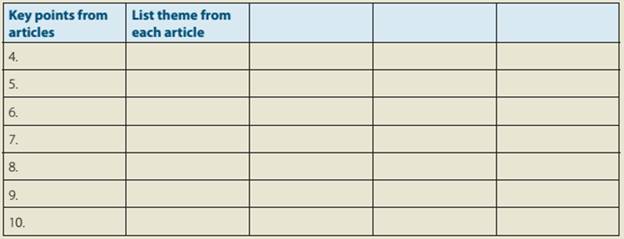
Then fill in these boxes.
Look at the underlying causes of the unethical behavior.
How often was a group?
How often an individual?
Want to see the full answer?
Check out a sample textbook solution
Chapter 4 Solutions
Understanding Management (MindTap Course List)
- Here's the authentic insight on the article that my classmate just wrote. Please give a brief comment about this. Thank you!arrow_forwardAt the end of 2014, a large university hospital in the Netherlands launched a procurement tender exercise for surgical suture material. The rationale for hospital management to initiate this procedure was cost-cutting and standardization. The award criteria were focussed on the most economically advantageous tender. There were different suppliers on the market that were able to produce and deliver high-quality surgical suture material for a lower price than was currently being paid. Consequently, the tender was awarded to a new supplier. The top managers and purchasing manager who initiated the tender trod carefully and implemented this relatively small-scale change initiative according to some basic change management principles (e.g. Kotter, 2012): they built a guiding coalition that incorporated renowned medical specialists, they consulted department heads and they communicated the change to surgeons through different channels. Furthermore, it was recorded in the tender that the new…arrow_forwardDiscuss Resistance to change and strategies that can be adopted to reduce resistance. Why people resist change? Include scholarly sources with the website links next to each point of information provided.arrow_forward
- Types of gestures include which of the following? Group of answer choices motions accents emblems posturearrow_forwardTypes of gestures include which of the following? Group of answer choices motions accents emblems posturearrow_forwardGestures and movement are examples of which type of nonverbals? Group of answer choices appearance proxemics vocalics kinesicsarrow_forward
- Is crowdfunding a good source for starting a financial planning company? Discuss why or why not it would be right for this.arrow_forwardSelect a company you might be interested in working for and go to their website. Take a look at their “Careers” or “Employment” link for Edward Jones. Determine what you like/dislike about their recruitment process. Is there good information available to the job seeker? Is there any information missing? What would you add/subtract from the website? Why? From the perspective of an HR professional, briefly share your findings and what you might do to improve it.arrow_forwardIn line with the case study, discuss the stages of Strategic Human Resources (HR) Planning. Outline ways in which HRprofessionals can align their strategies to cultivate a skilled and stable workforce, Drawing on the insights from progressivecompanies highlighted in the case study, detail the specific actions and considerations required at each stage of thestrategic HR planning process to effectively address these challenges and build a strong leadership pipeline, employeeengagement, and ESG-driven impact.arrow_forward
- you will act as a corporate secretarial team for a newly established public company, "TechGrowth Solutions Ltd." Your team must demonstrate practical application of meeting procedures, share registration processes, and administrative compliance. Project Requirements Meeting Management Portfolio Prepare a complete meeting package for the company's first Annual General Meeting, including: Notice of meeting with agenda Draft minutes template Register of members attendance Voting procedures documentation Post-meeting action items tracker Share Registration System Develop a comprehensive share registration system including: Share transfer procedures manual Templates for various share transfer forms Shareholder communication strategy Registration tracking system Administrative Compliance Framework Create an administrative compliance package containing: Compliance checklist for statutory requirements Schedule of required financial records Template for shareholder…arrow_forwardIf employees do not use the “open door” policy, it is probably because ______. Group of answer choices a negative listening environment exists they have nothing to discuss with the manager the administrative assistant is acting as a gatekeeper they are too busy to seek out the managerarrow_forwardPlease original work How Are We Doing? You are the new CEO of an up and coming startup. As you begin your job you are concerned about instilling a culture of innovation that will drive your company beyond its humble beginnings. In order to do that you realize that you need to really understand how well your technology initiatives are doing and have done in the past. Discuss how you can use Porter’s 5 Forces model to assist you in measuring your success or failure. Discuss how you can also use the Balanced Scorecard model to assist you in measuring your success or failure. Please cite in text references and add weblinksarrow_forward
 Understanding Management (MindTap Course List)ManagementISBN:9781305502215Author:Richard L. Daft, Dorothy MarcicPublisher:Cengage Learning
Understanding Management (MindTap Course List)ManagementISBN:9781305502215Author:Richard L. Daft, Dorothy MarcicPublisher:Cengage Learning Management, Loose-Leaf VersionManagementISBN:9781305969308Author:Richard L. DaftPublisher:South-Western College Pub
Management, Loose-Leaf VersionManagementISBN:9781305969308Author:Richard L. DaftPublisher:South-Western College Pub