
BIG JAVA: LATE OBJECTS
2nd Edition
ISBN: 9781119626220
Author: Horstmann
Publisher: WILEY
expand_more
expand_more
format_list_bulleted
Concept explainers
Textbook Question
Chapter 3, Problem 8PE
Write a
Expert Solution & Answer
Want to see the full answer?
Check out a sample textbook solution
Students have asked these similar questions
Solve in MATLAB
Hello please look at the attached picture. I need an detailed explanation of the architecture
Information Security Risk and Vulnerability Assessment
1- Which TCP/IP protocol is used to convert the IP address to the Mac address? Explain 2-What popular switch feature allows you to create communication boundaries between systems connected to the switch3- what types of vulnerability directly related to the programmer of the software?4- Who ensures the entity implements appropriate security controls to protect an asset?
Please do not use AI and add refrence
Chapter 3 Solutions
BIG JAVA: LATE OBJECTS
Ch. 3.1 - In some Asian countries, the number 14 is...Ch. 3.1 - Consider the following if statement to compute a...Ch. 3.1 - Prob. 3SCCh. 3.1 - Prob. 4SCCh. 3.1 - The variables fuel Amount and fuel Capacity hold...Ch. 3.2 - Which of the following conditions are true,...Ch. 3.2 - Prob. 7SCCh. 3.2 - What is the error in this statement? if (scoreA =...Ch. 3.2 - Supply a condition in this if statement to test...Ch. 3.2 - Prob. 10SC
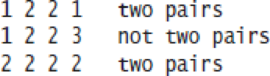
Ch. 3.3 - In a game program, the scores of players A and B...Ch. 3.3 - Prob. 12SCCh. 3.3 - Prob. 13SCCh. 3.3 - Beginners sometimes write statements such as the...Ch. 3.3 - Prob. 15SCCh. 3.3 - Suppose we want to have the earthquake program...Ch. 3.4 - Prob. 17SCCh. 3.4 - Would that amount change if the first nested if...Ch. 3.4 - Prob. 19SCCh. 3.4 - Prob. 20SCCh. 3.4 - Prob. 21SCCh. 3.5 - Draw a flowchart for a program that reads a value...Ch. 3.5 - Prob. 23SCCh. 3.5 - Prob. 24SCCh. 3.5 - Draw a flowchart for a program that reads a value...Ch. 3.5 - Draw a flowchart for a program that reads a value...Ch. 3.6 - Prob. 27SCCh. 3.6 - Prob. 28SCCh. 3.6 - Prob. 29SCCh. 3.6 - Suppose you are designing a part of a program for...Ch. 3.7 - Suppose x and y are two integers. How do you test...Ch. 3.7 - How do you test whether at least one of them is...Ch. 3.7 - How do you test whether exactly one of them is...Ch. 3.7 - Prob. 34SCCh. 3.7 - What is the advantage of using the type boolean...Ch. 3.8 - In the ElevatorSimulation2 program, what is the...Ch. 3.8 - Your task is to rewrite lines 1926 of the...Ch. 3.8 - In the Sherlock Holmes story The Adventure of the...Ch. 3.8 - Prob. 39SCCh. 3 - What is the value of each variable after the if...Ch. 3 - Prob. 2RECh. 3 - Find the errors in the following if statements. a....Ch. 3 - What do these code fragments print? a. int n = 1;...Ch. 3 - Suppose x and y are variables of type double....Ch. 3 - Suppose x and y are variables of type double....Ch. 3 - Explain why it is more difficult to compare...Ch. 3 - Given two pixels on a computer screen with integer...Ch. 3 - It is easy to confuse the - and operators. Write...Ch. 3 - Each square on a chess board can be described by a...Ch. 3 - Prob. 11RECh. 3 - In a scheduling program, we want to check whether...Ch. 3 - Draw a flowchart for the algorithm in Exercise...Ch. 3 - Draw a flowchart for the algorithm in Exercise...Ch. 3 - Draw a flowchart for the algorithm in Exercise...Ch. 3 - Prob. 16RECh. 3 - Prob. 17RECh. 3 - Write pseudocode for a program that prompts the...Ch. 3 - Write pseudocode for a program that assigns letter...Ch. 3 - Explain how the lexicographic ordering of strings...Ch. 3 - Of the following pairs of strings, which comes...Ch. 3 - Explain the difference between an if/else if/else...Ch. 3 - Give an example of an if/else if/else sequence...Ch. 3 - Rewrite the condition in Section 3.3 to use ...Ch. 3 - Prob. 25RECh. 3 - Make up a Java code example that shows the...Ch. 3 - Complete the following truth table by finding the...Ch. 3 - True or false? A B is the same as B A for any...Ch. 3 - The advanced search feature of many search engines...Ch. 3 - Suppose the value of b is false and the value of x...Ch. 3 - Simplify the following expressions. Here, b is a...Ch. 3 - Simplify the following statements. Here, b is a...Ch. 3 - What is wrong with the following program?...Ch. 3 - Write a program that reads an integer and prints...Ch. 3 - Write a program that reads a floating-point number...Ch. 3 - Write a program that reads an integer and prints...Ch. 3 - Write a program that reads three numbers and...Ch. 3 - Write a program that reads three numbers and...Ch. 3 - Repeat Exercise E3.5, but before reading the...Ch. 3 - Write a program that reads in three integers and...Ch. 3 - Write a program that reads four integers and...Ch. 3 - A compass needle points a given number of degrees...Ch. 3 - Write a program that reads a temperature value and...Ch. 3 - The boiling point of water drops by about one...Ch. 3 - Add error handling to Exercise E3.11. If the user...Ch. 3 - When two points in time are compared, each given...Ch. 3 - The following algorithm yields the season (Spring,...Ch. 3 - Write a program that reads in two floating-point...Ch. 3 - Unit conversion. Write a unit conversion program...Ch. 3 - Write a program that prompts the user to provide a...Ch. 3 - Write a program that asks the user to enter a...Ch. 3 - Write a program that translates a letter grade...Ch. 3 - Write a program that translates a number between 0...Ch. 3 - Write a program that takes user input describing a...Ch. 3 - Write a program that reads in three floating-point...Ch. 3 - Write a program that reads in three strings and...Ch. 3 - Write a program that prompts for the day and month...Ch. 3 - The original U.S. income tax of 1913 was quite...Ch. 3 - Write a program that computes taxes for the...Ch. 3 - The TaxReturn.java program uses a simplified...Ch. 3 - Write a program that reads in the x- and...Ch. 3 - Write a program that reads in the x- and...Ch. 3 - Write a program that reads in the x- and...Ch. 3 - Roman numbers. Write a program that converts a...Ch. 3 - A year with 366 days is called a leap year. Leap...Ch. 3 - French country names are feminine when they end...Ch. 3 - Write a program to simulate a bank transaction....Ch. 3 - Write a program that reads in the name and salary...Ch. 3 - When you use an automated teller machine (ATM)...Ch. 3 - Calculating the tip when you go to a restaurant is...Ch. 3 - A supermarket awards coupons depending on how much...Ch. 3 - Write a program that prompts the user for a...Ch. 3 - Repeat Exercise P3.21, modifying the program so...Ch. 3 - Repeat Exercise P3.21, modifying the program so...Ch. 3 - A minivan has two sliding doors. Each door can be...Ch. 3 - Sound level L in units of decibel (dB) is...Ch. 3 - The electric circuit shown below is designed to...Ch. 3 - Crop damage due to frost is one of the many risks...Ch. 3 - A mass m = 2 kilograms is attached to the end of a...Ch. 3 - The average person can jump off the ground with a...
Additional Engineering Textbook Solutions
Find more solutions based on key concepts
Sum of Numbers Write a method that accepts an integer argument and returns the sum of all the integers from 1 u...
Starting Out with Java: From Control Structures through Data Structures (4th Edition) (What's New in Computer Science)
Define a class called Diamond that is derived from either the class ShapeBasics (Listing 8.12) or the abstract ...
Java: An Introduction to Problem Solving and Programming (8th Edition)
102* The sum of seven interior angles ofa closed-polygon traverse each read to the nearest
3 ” is
$99 a 59 '39...
Elementary Surveying: An Introduction To Geomatics (15th Edition)
This optional Google account security feature sends you a message with a code that you must enter, in addition ...
SURVEY OF OPERATING SYSTEMS
ICA 8-45
A 10-gram [g] rubber ball is released from a height of 6 meters [m] above a flat surface on the moon. ...
Thinking Like an Engineer: An Active Learning Approach (4th Edition)
2D Array Operations Write a program that creates a two-dimensional array initialized with test data. Use any da...
Starting Out with C++ from Control Structures to Objects (9th Edition)
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Could you help me to know features of the following concepts: - commercial CA - memory integrity - WMI filterarrow_forwardBriefly describe the issues involved in using ATM technology in Local Area Networksarrow_forwardFor this question you will perform two levels of quicksort on an array containing these numbers: 59 41 61 73 43 57 50 13 96 88 42 77 27 95 32 89 In the first blank, enter the array contents after the top level partition. In the second blank, enter the array contents after one more partition of the left-hand subarray resulting from the first partition. In the third blank, enter the array contents after one more partition of the right-hand subarray resulting from the first partition. Print the numbers with a single space between them. Use the algorithm we covered in class, in which the first element of the subarray is the partition value. Question 1 options: Blank # 1 Blank # 2 Blank # 3arrow_forward
- 1. Transform the E-R diagram into a set of relations. Country_of Agent ID Agent H Holds Is_Reponsible_for Consignment Number $ Value May Contain Consignment Transports Container Destination Ф R Goes Off Container Number Size Vessel Voyage Registry Vessel ID Voyage_ID Tonnagearrow_forwardI want to solve 13.2 using matlab please helparrow_forwarda) Show a possible trace of the OSPF algorithm for computing the routing table in Router 2 forthis network.b) Show the messages used by RIP to compute routing tables.arrow_forward
- using r language to answer question 4 Question 4: Obtain a 95% standard normal bootstrap confidence interval, a 95% basic bootstrap confidence interval, and a percentile confidence interval for the ρb12 in Question 3.arrow_forwardusing r language to answer question 4. Question 4: Obtain a 95% standard normal bootstrap confidence interval, a 95% basic bootstrap confidence interval, and a percentile confidence interval for the ρb12 in Question 3.arrow_forwardusing r languagearrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage Learning
C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage Learning C++ for Engineers and ScientistsComputer ScienceISBN:9781133187844Author:Bronson, Gary J.Publisher:Course Technology Ptr
C++ for Engineers and ScientistsComputer ScienceISBN:9781133187844Author:Bronson, Gary J.Publisher:Course Technology Ptr Microsoft Visual C#Computer ScienceISBN:9781337102100Author:Joyce, Farrell.Publisher:Cengage Learning,
Microsoft Visual C#Computer ScienceISBN:9781337102100Author:Joyce, Farrell.Publisher:Cengage Learning, EBK JAVA PROGRAMMINGComputer ScienceISBN:9781337671385Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT
EBK JAVA PROGRAMMINGComputer ScienceISBN:9781337671385Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT Systems ArchitectureComputer ScienceISBN:9781305080195Author:Stephen D. BurdPublisher:Cengage LearningProgramming Logic & Design ComprehensiveComputer ScienceISBN:9781337669405Author:FARRELLPublisher:Cengage
Systems ArchitectureComputer ScienceISBN:9781305080195Author:Stephen D. BurdPublisher:Cengage LearningProgramming Logic & Design ComprehensiveComputer ScienceISBN:9781337669405Author:FARRELLPublisher:Cengage

C++ Programming: From Problem Analysis to Program...
Computer Science
ISBN:9781337102087
Author:D. S. Malik
Publisher:Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Course Technology Ptr

Microsoft Visual C#
Computer Science
ISBN:9781337102100
Author:Joyce, Farrell.
Publisher:Cengage Learning,

EBK JAVA PROGRAMMING
Computer Science
ISBN:9781337671385
Author:FARRELL
Publisher:CENGAGE LEARNING - CONSIGNMENT

Systems Architecture
Computer Science
ISBN:9781305080195
Author:Stephen D. Burd
Publisher:Cengage Learning

Programming Logic & Design Comprehensive
Computer Science
ISBN:9781337669405
Author:FARRELL
Publisher:Cengage
Constants, Variables, Data types, Keywords in C Programming Language Tutorial; Author: LearningLad;https://www.youtube.com/watch?v=d7tdL-ZEWdE;License: Standard YouTube License, CC-BY