
Concept explainers
For a function with prototype
long decoda2(long x, long y, long z);
GCC generates the following assembly code:
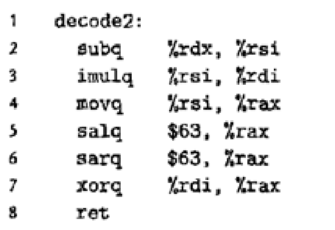
Parameters x, y, and z are passed in registers %rdi, %rsi, and %rdx. The code stores the return value in register %rax.
Write C code for decode2 that will have an effect equivalent to the assembly code shown.
Explanation of Solution
Given assembly code:
x in %rdi, y in %rsi and z in %rdx
decode2:
subq %rdx, %rsi
imulq %rsi, %rdi
movq %rsi, %rax
salq $63, %rax
sarq $63, %rax
xorq %rdi, %rax
ret
Load Effective Address:
- The load effective address instruction “leaq” is a variant of “movq” instruction.
- The instruction form reads memory to a register, but memory is not been referenced at all.
- The first operand of instruction is a memory reference; the effective address is been copied to destination.
- The pointers could be generated for later references of memory.
- The common arithmetic operations could be described compactly using this instruction.
- The operand in destination should be a register.
Data movement instructions:
- The different instructions are been grouped as “instruction classes”.
- The instructions in a class performs same operation but with different sizes of operand.
- The “Mov” class denotes data movement instructions that copy data from a source location to a destination.
- The class has 4 instructions that includes:
- movb:
- It copies data from a source location to a destination.
- It denotes an instruction that operates on 1 byte data size.
- movw:
- It copies data from a source location to a destination.
- It denotes an instruction that operates on 2 bytes data size.
- movl:
- It copies data from a source location to a destination.
- It denotes an instruction that operates on 4 bytes data size.
- movq:
- It copies data from a source location to a destination.
- It denotes an instruction that operates on 8 bytes data size.
- movb:
Comparison Instruction:
- The “CMP” instruction sets condition code according to differences of their two operands.
- The working pattern is same as “SUB” instruction but it sets condition code without updating destinations.
- The zero flag is been set if two operands are equal.
- The ordering relations between operands could be determined using other flags.
- The “cmpl” instruction compares values that are double word.
Unary and Binary Operations:
- The details of unary operations includes:
- The single operand functions as both source as well as destination.
- It can either be a memory location or a register.
- The instruction “incq” causes 8 byte element on stack top to be incremented.
- The instruction “decq” causes 8 byte element on stack top to be decremented.
- The details of binary operations includes:
- The first operand denotes the source.
- The second operand works as both source as well as destination.
- The first operand can either be an immediate value, memory location or register.
- The second operand can either be a register or a memory location.
Corresponding C code:
// Define method decode
long decode(long x, long y, long z)
{
// Declare variable
long tmp = y - z;
//Return
return (tmp * x)^(tmp << 63 >> 63);
}
Explanation:
- The register “%rdi” has value for “x”, register “%rsi” has value for “y” and register “%rdx” has value for “z”.
- The details of assembly code is shown below:
- The instruction “subq %rdx, %rsi” performs operation “y - z” and stores result in register “%rsi”.
- The statement “long tmp = y - z” corresponds to C code.
- The instruction “imulq %rsi, %rdi” multiplies result of operation with “x” and stores result in register “%rdi”.
- The statement “(tmp * x)” corresponds to C code.
- The instruction “movq %rsi, %rax” moves value in register “%rsi” to register “%rax”.
- The instruction “salq $63, %rax” performs left shift on value in register “%rax”.
- The statement “tmp << 63” corresponds to C code.
- The instruction “sarq $63, %rax” performs right shift on value in register “%rax”.
- The statement “tmp << 63 >> 63” corresponds to C code.
- The instruction “xorq %rdi, %rax” performs “XOR” operation on values in registers “%rax” and “%rdi”.
- The statement “return (tmp * x)^(tmp << 63 >> 63)” corresponds to C statement.
- The instruction “subq %rdx, %rsi” performs operation “y - z” and stores result in register “%rsi”.
Want to see more full solutions like this?
Chapter 3 Solutions
EBK COMPUTER SYSTEMS
Additional Engineering Textbook Solutions
Database Concepts (8th Edition)
Degarmo's Materials And Processes In Manufacturing
Starting Out with C++: Early Objects (9th Edition)
Starting Out with C++ from Control Structures to Objects (9th Edition)
Starting Out with Java: From Control Structures through Data Structures (4th Edition) (What's New in Computer Science)
Java: An Introduction to Problem Solving and Programming (8th Edition)
- This battle room is focused on entry level tasks for a network analyst where you will be given trials and reconnaissance, sensor tuning, log aggregation, SIEM queries, and network analysis. For this week’s project, complete the following tasks: From your Project Ares portal, LOG IN Click on LAUNCH GAME. Select the region NORTH AMERICA Click on Battle School Under the BATTLE SCHOOL pop-up window, click on START TRAINING. Under the BATTLE ROOMS tile, click on ENTER. Under the NETWORK ANALYST tile, click on PLAY. Wait for the Battle Room to load. While loading, the BATTLE ROOM button will display red. Once the Battle Room is loaded, the BATTLE ROOM button will turn yellow and the center of the disk display will indicate CONNECTED. Click on the BATTLE ROOM button to enter the Battle Room. Below the TASKS folder, make sure you click on INSTRUCTIONS to download the Network Analyst Fundamentals material. In the Battle Room, under the TASKS menu select task INTRUSION DETECTION. Complete…arrow_forwardCreate a relationship between the common field (Technician Number) of the two tables. Make sure that each client must have 1 and only 1 technician assigned, and each technician can have multiple clients. 2. Create a query to show the Client Number, Client Name, Billed, Paid for clients in Anderson city. Save the query. 3. Create a query to show the Technician Number, Last Name, First Name, YTD Earnings for technicians whose Hourly Rate is greater than or equal to 30. Save the query. 4. Create a query to show Client Number, Client Name, Billed, Paid for clients whose technician number is 22 and whose Billed is over 300. Save the query. 5. Create a query to show the Technician Number, Last Name, First Name, Client Number, Client Name for clients whose technician number 23. Save the query. 6. Create a query to show the Technician Number, Last Name, First Name, Client Number, Client Name for clients whose technician number 23 or 29. Save the query Help please Microsoft office accessarrow_forwardDijkstra's Algorithm (part 1). Consider the network shown below, and Dijkstra’s link-state algorithm. Here, we are interested in computing the least cost path from node E (note: the start node here is E) to all other nodes using Dijkstra's algorithm. Using the algorithm statement used in the textbook and its visual representation, complete the "Step 0" row in the table below showing the link state algorithm’s execution by matching the table entries (i), (ii), (iii), and (iv) with their values. Write down your final [correct] answer, as you‘ll need it for the next question.arrow_forward
 C++ for Engineers and ScientistsComputer ScienceISBN:9781133187844Author:Bronson, Gary J.Publisher:Course Technology Ptr
C++ for Engineers and ScientistsComputer ScienceISBN:9781133187844Author:Bronson, Gary J.Publisher:Course Technology Ptr C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage LearningCOMPREHENSIVE MICROSOFT OFFICE 365 EXCEComputer ScienceISBN:9780357392676Author:FREUND, StevenPublisher:CENGAGE L
C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage LearningCOMPREHENSIVE MICROSOFT OFFICE 365 EXCEComputer ScienceISBN:9780357392676Author:FREUND, StevenPublisher:CENGAGE L Microsoft Visual C#Computer ScienceISBN:9781337102100Author:Joyce, Farrell.Publisher:Cengage Learning,
Microsoft Visual C#Computer ScienceISBN:9781337102100Author:Joyce, Farrell.Publisher:Cengage Learning, EBK JAVA PROGRAMMINGComputer ScienceISBN:9781337671385Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT
EBK JAVA PROGRAMMINGComputer ScienceISBN:9781337671385Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT Systems ArchitectureComputer ScienceISBN:9781305080195Author:Stephen D. BurdPublisher:Cengage Learning
Systems ArchitectureComputer ScienceISBN:9781305080195Author:Stephen D. BurdPublisher:Cengage Learning





