
Computer Science: An Overview (13th Edition) (What's New in Computer Science)
13th Edition
ISBN: 9780134875583
Author: BROOKSHEAR
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Question
Chapter 10, Problem 27CRP
Program Plan Intro
View volume:
It is a setup which is used to view image of object projected on the image window, the corners of window is within the range of projectors.
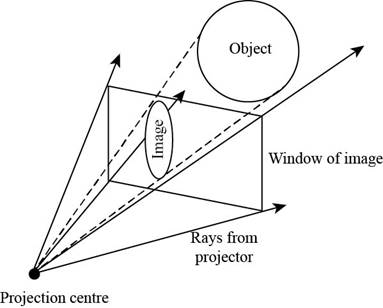
Window of image is used as a window to view the final image of the object.
Expert Solution & Answer
Want to see the full answer?
Check out a sample textbook solution
Students have asked these similar questions
I would like to know the features of BranchCache, Metadata, and LPR Port Monitor
Please answer the JAVA OOP questions below:
How do arrays of objects differ from arrays of primitive types?
Why and when would you use an array of objects?
What are the different ways to initialize an array of objects?
What is a static variable in Java? How does its scope differ from instance variables?
When should you use static variables? Provide examples where static variables are beneficial over instance variables.
What is the difference between static and non-static methods in the Data Definition Class? What are the benefits of using static methods?
Assume you are a loyal member of Costco. You have been expecting your membership reward from the company, and you just received a text message on your mobile phone. The message appears to be from Costco:
Costco - Your 3% return is ready: costco.wholesaledividend.com
Before clicking the link in the message, you consider whether this is genuinely from Costco or a phishing attack on you. How can you tell? If it is a phishing attack, what mechanism was most likely used to send the message to you? What actions can you take if you are not sure whether it is a genuine message from Costco? What actions can you take if you are sure this is a phishing attack?
Chapter 10 Solutions
Computer Science: An Overview (13th Edition) (What's New in Computer Science)
Ch. 10.1 - Prob. 1QECh. 10.1 - Prob. 2QECh. 10.1 - Prob. 3QECh. 10.2 - Prob. 1QECh. 10.2 - Prob. 2QECh. 10.2 - Prob. 3QECh. 10.3 - Prob. 1QECh. 10.3 - Prob. 2QECh. 10.3 - Prob. 3QECh. 10.3 - Prob. 4QE
Ch. 10.3 - Prob. 5QECh. 10.4 - Prob. 1QECh. 10.4 - Prob. 2QECh. 10.4 - Prob. 3QECh. 10.4 - Prob. 4QECh. 10.4 - Prob. 5QECh. 10.5 - Prob. 1QECh. 10.5 - Prob. 2QECh. 10.5 - Prob. 3QECh. 10.5 - Prob. 4QECh. 10.6 - Prob. 1QECh. 10.6 - What is a storyboard?Ch. 10.6 - Prob. 3QECh. 10.6 - Prob. 4QECh. 10 - Prob. 1CRPCh. 10 - Prob. 2CRPCh. 10 - Prob. 3CRPCh. 10 - Prob. 4CRPCh. 10 - Prob. 5CRPCh. 10 - Prob. 6CRPCh. 10 - Prob. 7CRPCh. 10 - Prob. 8CRPCh. 10 - Prob. 9CRPCh. 10 - Prob. 10CRPCh. 10 - Prob. 11CRPCh. 10 - Prob. 12CRPCh. 10 - Prob. 13CRPCh. 10 - Prob. 14CRPCh. 10 - Prob. 15CRPCh. 10 - Prob. 16CRPCh. 10 - Prob. 17CRPCh. 10 - Prob. 18CRPCh. 10 - Prob. 19CRPCh. 10 - Prob. 20CRPCh. 10 - Prob. 21CRPCh. 10 - Prob. 22CRPCh. 10 - Prob. 23CRPCh. 10 - Prob. 24CRPCh. 10 - Prob. 25CRPCh. 10 - Prob. 26CRPCh. 10 - Prob. 27CRPCh. 10 - Prob. 28CRPCh. 10 - Prob. 29CRPCh. 10 - Prob. 30CRPCh. 10 - Prob. 31CRPCh. 10 - Prob. 32CRPCh. 10 - Prob. 33CRPCh. 10 - In what way does the hardware in a computer...Ch. 10 - Prob. 35CRPCh. 10 - Prob. 36CRPCh. 10 - Prob. 37CRPCh. 10 - Prob. 38CRPCh. 10 - Prob. 39CRPCh. 10 - Prob. 40CRPCh. 10 - Prob. 41CRPCh. 10 - Prob. 42CRPCh. 10 - Prob. 43CRPCh. 10 - Prob. 44CRPCh. 10 - Prob. 1SICh. 10 - The following questions are intended as a guide to...Ch. 10 - Prob. 3SICh. 10 - Prob. 4SI
Knowledge Booster
Similar questions
- RSA and Diffie-Hellman are important algorithms in public-key cryptography. What are the differences between the two? Assume you intercept the ciphertext C = 105 sent to a user whose public key is e = 7, n = 403. Explain in detail how you will find the private key of the user and crack the ciphertext. What is the plaintext M?arrow_forwardCBC-Pad is a block cipher mode of operation commonly used in block ciphers. CBC-Pad handles plain text of any length. Padding is used to ensure that the plaintext input is a multiple of the block length. Hence, the ciphertext is longer than the plaintext by at most the size of a single block.Assume that the original plaintext is 556 bytes and the size of a cipher block is 28 bytes. What will be the padding? If the original plaintext is an integer multiple of the block size, will padding still be needed? Why or why not?arrow_forwardAbstract classes & Interfaces (Ch13) 5. See the code below and solve the following. class Circle { protected double radius; // Default constructor public Circle() ( } this(1.0); // Construct circle with specified radius public Circle(double radius) { } this.radius radius; // Getter method for radius public double getRadius() { } return radius; // Setter method for radius public void setRadius(double radius) { } this.radius = radius; // Implement the findArea method defined in GeometricObject public double findArea() { } return radius* radius * Math. PI; // Implement the find Perimeter method defined in GeometricObject public double findPerimeter() { } return 2*radius*Math.PI; // Override the equals() method defined in the Object class public boolean equals(Circlel circle) { } return this.radius == circle.getRadius(); // Override the toString() method defined in the Object class public String toString() { } } return "[Circle] radius = " + radius; 5-1. Define a class name…arrow_forward
- 6. What is Race condition? How to prevent it? [2 marks] 7. How many synchronization methods do you know and compare the differences. [2 marks] 8. Explain what are the “mutual exclusion”, “deadlock”, “livelock”, and “eventual entry”, with the traffic intersection as an example like dinning philosophy. [2 marks] 9. For memory allocation, what are the difference between internal fragmentation and external fragmentation. Explain with an example. [2 marks] 10. How can the virtual memory map to the physical memory. Explain with an example. [2 marks]arrow_forwardYour answers normally have 50 words. Less than 50 words will not get marks. 1. What is context switch between multiple processes? [2 marks] 2. Draw the memory layout for a C program. [2 marks] 3. How many states does a process has? [2 marks] 4. Compare the non-preemptitve scheduling and preemptive scheduling. [2 marks] 5. Given 4 process and their arrival times and next CPU burst times, what are the average times and average Turnaround time, for different scheduling algorithms including: a. First Come, First-Served (FCFS) Scheduling [2 marks] b. Shortest-Job-First (SJF) Scheduling [2 marks] c. Shortest-remaining-time-first [2 marks] d. Priority Scheduling [2 marks] e. Round Robin (RR) [2 marks] Process Arrival Time Burst Time P1 0 8 P2 1 9 P3 3 2 P4 5 4arrow_forwarda database with multiple tables from attributes as shown above that are in 3NF, showing PK, non-key attributes, and FK for each table? Assume the tables are already in 1NF. [Hint: 3 tables will result after deducing 1NF -> 2NF -> 3NF]arrow_forward
- a database with multiple tables from attributes as shown above that are in 3NF, showing PK, non-key attributes, and FK for each table? Assume the tables are already in 1NF. [Hint: 3 tables will result after deducing 1NF -> 2NF -> 3NF]arrow_forwardIf a new entity Order_Details is introduced, will it be a strong entity or weak entity? If it is a weak entity, then mention its type (ID or Non-ID, also Justify why)?arrow_forwardWhich one of the 4 Entities mention in the diagram can have a recursive relationship? Order, Product, store, customer.arrow_forward
- Inheritance & Polymorphism (Ch11) There are 6 classes including Person, Student, Employee, Faculty, and Staff. 4. Problem Description: • • Design a class named Person and its two subclasses named student and Employee. • Make Faculty and Staff subclasses of Employee. • A person has a name, address, phone number, and e-mail address. • • • A person has a class status (freshman, sophomore, junior and senior). Define the status as a constant. An employee has an office, salary, and date hired. A faculty member has office hours and a rank. A staff member has a title. Override the toString() method in each class to display the class name and the person's name. 4-1. Explain on how you would code this program. (1 point) 4-2. Implement the program. (2 point) 4-3. Explain your code. (2 point)arrow_forwardSuppose you buy an electronic device that you operate continuously. The device costs you $300 and carries a one-year warranty. The warranty states that if the device fails during its first year of use, you get a new device for no cost, and this new device carries exactly the same warranty. However, if it fails after the first year of use, the warranty is of no value. You plan to use this device for the next six years. Therefore, any time the device fails outside its warranty period, you will pay $300 for another device of the same kind. (We assume the price does not increase during the six-year period.) The time until failure for a device is gamma distributed with parameters α = 2 and β = 0.5. (This implies a mean of one year.) Use @RISK to simulate the six-year period. Include as outputs (1) your total cost, (2) the number of failures during the warranty period, and (3) the number of devices you own during the six-year period. Your expected total cost to the nearest $100 is _________,…arrow_forwardWhich one of the 4 Entities mention in the diagram can have a recursive relationship? If a new entity Order_Details is introduced, will it be a strong entity or weak entity? If it is a weak entity, then mention its type (ID or Non-ID, also Justify why)?arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 New Perspectives on HTML5, CSS3, and JavaScriptComputer ScienceISBN:9781305503922Author:Patrick M. CareyPublisher:Cengage Learning
New Perspectives on HTML5, CSS3, and JavaScriptComputer ScienceISBN:9781305503922Author:Patrick M. CareyPublisher:Cengage Learning Systems ArchitectureComputer ScienceISBN:9781305080195Author:Stephen D. BurdPublisher:Cengage Learning
Systems ArchitectureComputer ScienceISBN:9781305080195Author:Stephen D. BurdPublisher:Cengage Learning- Np Ms Office 365/Excel 2016 I NtermedComputer ScienceISBN:9781337508841Author:CareyPublisher:Cengage
 Principles of Information Systems (MindTap Course...Computer ScienceISBN:9781285867168Author:Ralph Stair, George ReynoldsPublisher:Cengage LearningCOMPREHENSIVE MICROSOFT OFFICE 365 EXCEComputer ScienceISBN:9780357392676Author:FREUND, StevenPublisher:CENGAGE L
Principles of Information Systems (MindTap Course...Computer ScienceISBN:9781285867168Author:Ralph Stair, George ReynoldsPublisher:Cengage LearningCOMPREHENSIVE MICROSOFT OFFICE 365 EXCEComputer ScienceISBN:9780357392676Author:FREUND, StevenPublisher:CENGAGE L


New Perspectives on HTML5, CSS3, and JavaScript
Computer Science
ISBN:9781305503922
Author:Patrick M. Carey
Publisher:Cengage Learning

Systems Architecture
Computer Science
ISBN:9781305080195
Author:Stephen D. Burd
Publisher:Cengage Learning

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:9781337508841
Author:Carey
Publisher:Cengage

Principles of Information Systems (MindTap Course...
Computer Science
ISBN:9781285867168
Author:Ralph Stair, George Reynolds
Publisher:Cengage Learning

COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
Computer Science
ISBN:9780357392676
Author:FREUND, Steven
Publisher:CENGAGE L