
Explanation of Solution
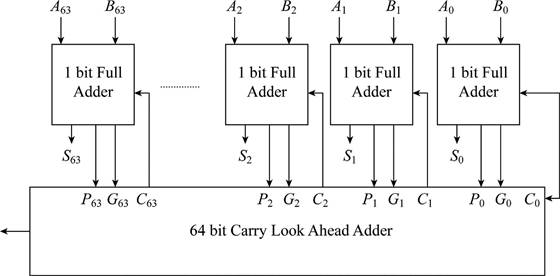
- The above diagram describes about the 64 bit carry look ahead adder that includes 64 numbers of 1-bit full adders to add the 64 bits.
- It includes carry generator, carry propagator and sum.
- Carry generator denoted by G is used for generating the output query without depending on input query.
- Carry propagator denoted by P is used for propagating the next state.
- The sum of each adder is denoted by S.
From the above diagram, the carry propagator (P) and carry generator (G) are calculated as follows
Then, the sum of the each adder can be calculated as follows
Thus, the required equation is
Substitute, “0” for “I” in the equation (1)
The first equation can be calculated as follows
The first equation with the new notation is
Thus, the first equation with the new notation for 64 bit is
The second equation can be calculated as follows
Substitute, “
The second equation with new notation is
Thus, the second equation with new notation for 64 bit is
The third equation can be calculated as follows
Substitute, “
The third equation with new notation is
Thus, the third equation with new notation for 64 bit is
The fourth equation can be calculated as follows
Substitute, “
The fourth equation with new notation is
Thus, the fourth equation with new notation for 64 bit is
Want to see more full solutions like this?
Chapter B Solutions
COMPUTER ORGANIZATION+DESIGN >I<
- 2. Jane, Jill, and Jenny have formed a band consisting of 3 instruments. (a) If each of them can play all 3 instruments, how many different arrangements are possible? (b) What if Jane can play all 3 instruments, but Jill and Jenny can each play only piano and drums?arrow_forward4. A person has 9 friends, of whom 5 will be invited to a party. (a) How many choices are there if 2 of the friends are feuding and will not attend together? (b) How many choices if 2 of the friends will only attend together?arrow_forward5. There are 3 people in a room, and we are curious whether two of them have their birthday in the same month. We record the triplet that describes the month of birthday for each person. E.g., (Oct, Jan, Jul) is one possible triplet/outcome. (Since each month applies to a specific person, (Oct, Jan, Jul) is not the same as (Jan, Jul, Oct), so order is important.) (a) How many possible outcomes are there? (b) In how many of these outcomes do all three people have their birthday in different months? (c) In how many of these outcomes do at least two people have their birthday in the same month?arrow_forward
- 1. We have 8 blocks, of which 4 are green, 2 are red, 1 is white, and 1 is black. If we put the blocks in a line, how many arrangements are possible?arrow_forward3. (a) In how many ways can 3 cats and 3 dogs sit in a row? (b) In how many ways can 3 cats and 3 dogs sit in a row if the cats and the dogs are each to sit together? (c) In how many ways if only the cats must sit together? (d) In how many ways if no two animals of the same type are allowed to sit together?arrow_forwardthe gate level and the transistor level for a certain circuit are given below. Select from the given options for each space the variable name such that the transistor level design matches the gate level design. $1 => S2= M- W $3= |S4 = $5= J -R S1. S2- R S5 S3 S4arrow_forward
- Given that W, L. and tox are scaled with a scaling factor J, Vth and Vad are scaled with a scaling factor P Taking these scaling factors into consideration what is the scaling factor for metric X that equals loN C where loN is the on current of the transistor and C is the gate capacitance of the transistor. O p²/j2 O 1/P O J/P O 1/J2 O P/J2 O 1/(JP) O 1/p2 O P/J O 1/J2 O None of the other optionsarrow_forwardpython Tasks 7 • Task 1: Add a new class 'Moon` that inherits from `CelestialBody' and has an additional attribute `parent_planet. Write a method to display the moon's details along with its parent planet. • Task 2: Modify the 'Galaxy' class to calculate the total mass of all celestial bodies it contains. Implement a method `total_mass() for this purpose. • Task 3: Create a class 'BlackHole` that inherits from `Celestial Body` and adds properties like event_horizon_radius' and 'spins. Implement a method to display black hole details. • Task 4: Develop a simulation where a user can create multiple galaxies and display their celestial bodies in a hierarchical format using inheritance. 10/06/1446arrow_forwardPlease solve q2arrow_forward
- self.sAge = age super().__init_("Rahul", age) # inheriting the properties of def displayInfo(self): print(self.sName, self.sAge) obj = Student("Mayank", 23) obj.display() obj.displayInfo() parent class we created the object 'obj' of the child class. When we called the constructor of the child class 'Student', it initialized the data members to the values passed during the object creation. Then using the super() function, we invoked the constructor of the parent class. Asst.L. Manar Hamza Bashaa 2024-2arrow_forwardObject-oriented programming tion defines a new type of that class. Lec 7: Static Members Object-Oriented Programming Assignment: Create a class named StudentRecords and add a static variable named records, which is a list shared among all objects of the class. Then add a method named add_record that takes a student's name as input and appends it to the shared records list.arrow_forwardpython Tasks 6 • Task 1: Develop a Student Profile class with private attributes for `name` and __ grades` (a list of grades), and methods to add a grade and calculate the average. • Task 2: Create a `Playlist class that stores song titles in a private list, with methods to add a song, remove a song, and display the current playlist. • Task 3: Implement a `Temperature Sensor class with a private `_temperature attribute, and methods to set and get the temperature in both Celsius and Fahrenheit. • Task 4: Build a Library Book class with private attributes for the title and availability status; include methods to check out, return, and display the book's availability ⚫Task 5(homework): Create a 'Counter` class with a private _ count attribute, and include get_count()` and `set_count(value)` methods to access and modify it. Ensure set_count only accepts non-negative integers, and add increment()', decrement(), and reset()` methods for control.arrow_forward
 Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON
Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science
Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning
Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning
Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education
Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY
Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY





