EBK STARTING OUT WITH VISUAL C#
5th Edition
ISBN: 9780135204818
Author: GADDIS
Publisher: VST
expand_more
expand_more
format_list_bulleted
Concept explainers
Textbook Question
Chapter 4, Problem 1PP
Roman Numeral Converter
Create an application that allows the user to enter an integer between 1 and 10 into a TextBox control. The
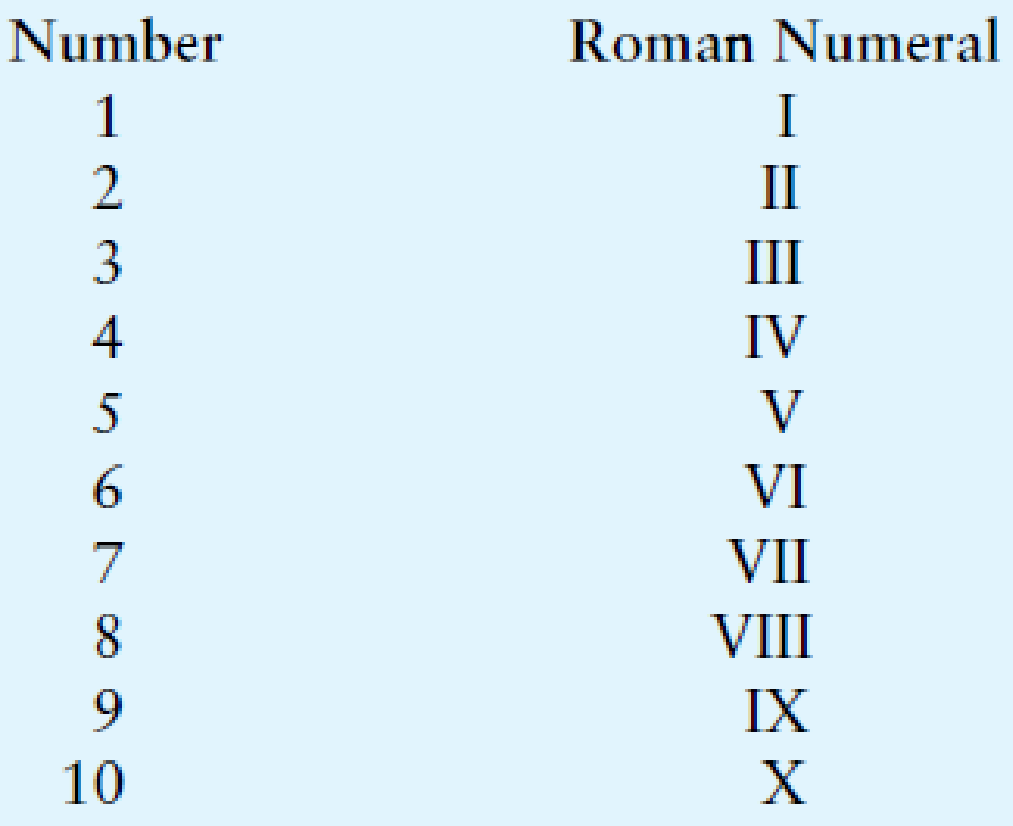
The following table lists the Roman numerals for the numbers 1 through 10.
Expert Solution & Answer
Learn your wayIncludes step-by-step video

schedule08:37
Students have asked these similar questions
Considering the TM example of binary sum ( see attached)do the step-by-step of execution for the binary numbers 1101 and 11.
Feel free to use the Formal Language Editor Tool to execute it;
Write it down the current state of the tape (including the head position) and indicate the current state of the TM at each step.
I need help on inculding additonal code where I can can do the opposite code of MatLab, where the function of t that I enter becomes the result of F(t), in other words, turning the time-domain f(t) into the frequency-domain function F(s):
I need help with the TM computation step-by-step execution for the binary numbers 1101 and 11.
Formal Language Editor Tool can be used to execute it; Write it down the current state of the tape (including the head position) and indicate the current state of the TM at each step;
Chapter 4 Solutions
EBK STARTING OUT WITH VISUAL C#
Ch. 4.1 - What is a control structure?Ch. 4.1 - What is a decision structure?Ch. 4.1 - Prob. 4.3CPCh. 4.1 - Prob. 4.4CPCh. 4.1 - What types of relationships between numeric values...Ch. 4.1 - Write an if statement that determines whether the...Ch. 4.1 - Write an if statement that determines whether the...Ch. 4.2 - Prob. 4.8CPCh. 4.2 - In an if-else statement, under what circumstances...Ch. 4.2 - Write an if-else statement that works like this:...
Ch. 4.3 - Convert the following set of nested if-else...Ch. 4.4 - Prob. 4.12CPCh. 4.4 - Prob. 4.13CPCh. 4.4 - Assume the variables a = 2, b = 4, and c = 6....Ch. 4.4 - Explain how short-circuit evaluation works with...Ch. 4.4 - Write an if statement that displays the message...Ch. 4.4 - Write an if statement that displays the message...Ch. 4.5 - Prob. 4.18CPCh. 4.5 - Prob. 4.19CPCh. 4.6 - If the following code were part of a complete...Ch. 4.6 - If the following code were part of a complete...Ch. 4.7 - Prob. 4.22CPCh. 4.7 - If a TryParse method successfully converts the...Ch. 4.7 - Prob. 4.24CPCh. 4.7 - Prob. 4.25CPCh. 4.9 - Prob. 4.26CPCh. 4.9 - If several CheckBox controls have been created in...Ch. 4.9 - Prob. 4.28CPCh. 4.10 - Convert the following if-else-if code to a switch...Ch. 4.11 - Prob. 4.30CPCh. 4.11 - Prob. 4.31CPCh. 4.11 - Prob. 4.32CPCh. 4 - A __________ structure executes a set of...Ch. 4 - A __________ structure provides one alternative...Ch. 4 - A(n) __________ expression has a value of either...Ch. 4 - The symbols , , and == are all __________...Ch. 4 - A __________ structure tests a condition and then...Ch. 4 - You use a(n) __________ statement to write a...Ch. 4 - You use a(n) __________ statement to write a dual...Ch. 4 - A ____________ decision structure is written...Ch. 4 - , ||, and ! are __________ operators. a....Ch. 4 - A compound Boolean expression created with the...Ch. 4 - A compound Boolean expression created with the...Ch. 4 - The __________ operator takes a Boolean expression...Ch. 4 - A __________ is a Boolean variable that signals...Ch. 4 - Prob. 14MCCh. 4 - Prob. 15MCCh. 4 - Prob. 16MCCh. 4 - The __________ section of a switch statement is...Ch. 4 - A ListBoxs index numbering starts at __________....Ch. 4 - You can use the __________ property to determine...Ch. 4 - The __________ property holds the item that is...Ch. 4 - Prob. 1TFCh. 4 - A single-alternative decision structure tests a...Ch. 4 - The if-else statement is a dual-alternative...Ch. 4 - A decision structure can be nested inside another...Ch. 4 - A compound Boolean expression created with the ...Ch. 4 - Prob. 6TFCh. 4 - Multiple CheckBox controls in the same GroupBox...Ch. 4 - The test expression in a switch statement can be a...Ch. 4 - If an item is not selected in a ListBox, the...Ch. 4 - Prob. 10TFCh. 4 - What is meant by the term conditionally executed?Ch. 4 - You need to test a condition and then execute one...Ch. 4 - Briefly describe how the operator works.Ch. 4 - Briefly describe how the || operator works.Ch. 4 - Prob. 5SACh. 4 - What is a flag and how does it work?Ch. 4 - What are the two arguments that you pass to a...Ch. 4 - How do you determine in code whether a RadioButton...Ch. 4 - Prob. 9SACh. 4 - Prob. 10SACh. 4 - Write an if statement that assigns 20 to the...Ch. 4 - Write an if statement that assigns 0 to the...Ch. 4 - Write an if-else statement that assigns 0 to the...Ch. 4 - Write nested decision structures that perform the...Ch. 4 - Write an if-else statement that displays Speed is...Ch. 4 - Write an if-else statement that determines whether...Ch. 4 - Prob. 7AWCh. 4 - Rewrite the following if-else-if statement as a...Ch. 4 - Prob. 9AWCh. 4 - Roman Numeral Converter Create an application that...Ch. 4 - Mass and Weight Scientists measure an objects mass...Ch. 4 - Magic Dates The date June 10, 1960, is special...Ch. 4 - Color Mixer The colors red, blue, and yellow are...Ch. 4 - Prob. 5PPCh. 4 - Book Club Points Serendipity Booksellers has a...Ch. 4 - Software Sales A software company sells a package...Ch. 4 - Body Mass Index Program Enhancement In Programming...Ch. 4 - Change for a Dollar Game Create a change-counting...Ch. 4 - Fat Percentage Calculator One gram of fat has 9...Ch. 4 - Time Calculator Create an application that lets...Ch. 4 - Workshop Selector The following table shows a...
Additional Engineering Textbook Solutions
Find more solutions based on key concepts
Compare and contrast the while and for iteration statements.
Java How to Program, Early Objects (11th Edition) (Deitel: How to Program)
What modification must be incorporated into a cutting torch to permit it to cut metal under water?
Degarmo's Materials And Processes In Manufacturing
Assume a telephone signal travels through a cable at two-thirds the speed of light. How long does it take the s...
Electric Circuits. (11th Edition)
Consider the example code shown in Figure 7-10. What changes would you need to make to ensure that the applicat...
Modern Database Management
Give a statement that will close the stream toFile created for the previous two questions.
Java: An Introduction to Problem Solving and Programming (8th Edition)
What is a ToolTip?
Starting Out With Visual Basic (8th Edition)
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Ensure you answer the question asked at the end of the document. Do not just paste things without the GNS3 console outputsarrow_forward"Do not use AI tools. Solve the problem by hand on paper only and upload a photo of your handwritten solution."arrow_forward"Do not use AI tools. Solve the problem by hand on paper only and upload a photo of your handwritten solution."arrow_forward
- "Do not use AI tools. Solve the problem by hand on paper only and upload a photo of your handwritten solution."arrow_forward"Do not use AI tools. Solve the problem by hand on paper only and upload a photo of your handwritten solution."arrow_forwardSolve this "Do not use AI tools. Solve the problem by hand on paper only and upload a photo of your handwritten solution."arrow_forward
- "Do not use AI tools. Solve the problem by hand on paper only and upload a photo of your handwritten solution."arrow_forward"Do not use AI tools. Solve the problem by hand on paper only and upload a photo of your handwritten solution."arrow_forwardSpecifications: Part-1Part-1: DescriptionIn this part of the lab you will build a single operation ALU. This ALU will implement a bitwise left rotation. Forthis lab assignment you are not allowed to use Digital's Arithmetic components.IF YOU ARE FOUND USING THEM, YOU WILL RECEIVE A ZERO FOR LAB2!The ALU you will be implementing consists of two 4-bit inputs (named inA and inB) and one 4-bit output (named out). Your ALU must rotate the bits in inA by the amount given by inB (i.e. 0-15).Part-1: User InterfaceYou are provided an interface file lab2_part1.dig; start Part-1 from this file.NOTE: You are not permitted to edit the content inside the dotted lines rectangle. Part-1: ExampleIn the figure above, the input values that we have selected to test are inA = {inA_3, inA_2, inA_1, inA_0} = {0, 1, 0,0} and inB = {inB_3, inB_2, inB_1, inB_0} = {0, 0, 1, 0}. Therefore, we must rotate the bus 0100 bitwise left by00102, or 2 in base 10, to get {0, 0, 0, 1}. Please note that a rotation left is…arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Programming with Microsoft Visual Basic 2017Computer ScienceISBN:9781337102124Author:Diane ZakPublisher:Cengage LearningProgramming Logic & Design ComprehensiveComputer ScienceISBN:9781337669405Author:FARRELLPublisher:Cengage
Programming with Microsoft Visual Basic 2017Computer ScienceISBN:9781337102124Author:Diane ZakPublisher:Cengage LearningProgramming Logic & Design ComprehensiveComputer ScienceISBN:9781337669405Author:FARRELLPublisher:Cengage Microsoft Visual C#Computer ScienceISBN:9781337102100Author:Joyce, Farrell.Publisher:Cengage Learning,
Microsoft Visual C#Computer ScienceISBN:9781337102100Author:Joyce, Farrell.Publisher:Cengage Learning, EBK JAVA PROGRAMMINGComputer ScienceISBN:9781305480537Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT
EBK JAVA PROGRAMMINGComputer ScienceISBN:9781305480537Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage Learning
C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage Learning EBK JAVA PROGRAMMINGComputer ScienceISBN:9781337671385Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT
EBK JAVA PROGRAMMINGComputer ScienceISBN:9781337671385Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:9781337102124
Author:Diane Zak
Publisher:Cengage Learning

Programming Logic & Design Comprehensive
Computer Science
ISBN:9781337669405
Author:FARRELL
Publisher:Cengage

Microsoft Visual C#
Computer Science
ISBN:9781337102100
Author:Joyce, Farrell.
Publisher:Cengage Learning,

EBK JAVA PROGRAMMING
Computer Science
ISBN:9781305480537
Author:FARRELL
Publisher:CENGAGE LEARNING - CONSIGNMENT

C++ Programming: From Problem Analysis to Program...
Computer Science
ISBN:9781337102087
Author:D. S. Malik
Publisher:Cengage Learning

EBK JAVA PROGRAMMING
Computer Science
ISBN:9781337671385
Author:FARRELL
Publisher:CENGAGE LEARNING - CONSIGNMENT
Control Structure in Data Structure - Data Structures - Computer Science Class 12; Author: Ekeeda;https://www.youtube.com/watch?v=9FTw2pXLhv4;License: Standard YouTube License, CC-BY