
Introduction To Programming Using Visual Basic (11th Edition)
11th Edition
ISBN: 9780135416037
Author: David I. Schneider
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Textbook Question
Chapter 3.2, Problem 53E
In the following exercises, write a
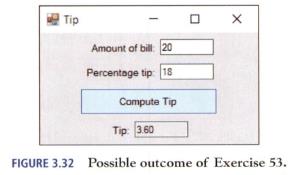
Server's Tip Calculate the amount of a server's tip, given the amount of the bill and the percentage tip as input. See Fig. 3.32.
Expert Solution & Answer
Want to see the full answer?
Check out a sample textbook solution
Students have asked these similar questions
Solve this
"Do not use AI tools. Solve the problem by hand on paper only and upload a photo of your handwritten solution."
Solve this
"Do not use AI tools. Solve the problem by hand on paper only and upload a photo of your handwritten solution."
Solve this
"Do not use AI tools. Solve the problem by hand on paper only and upload a photo of your handwritten solution."
Chapter 3 Solutions
Introduction To Programming Using Visual Basic (11th Edition)
Ch. 3.1 - Prob. 1ECh. 3.1 - Prob. 2ECh. 3.1 - Prob. 3ECh. 3.1 - Prob. 4ECh. 3.1 - Prob. 5ECh. 3.1 - Prob. 6ECh. 3.1 - Prob. 7ECh. 3.1 - Prob. 8ECh. 3.1 - Prob. 9ECh. 3.1 - Prob. 10E
Ch. 3.1 - Prob. 11ECh. 3.1 - Prob. 12ECh. 3.1 - Prob. 13ECh. 3.1 - Prob. 14ECh. 3.1 - Prob. 15ECh. 3.1 - Prob. 16ECh. 3.1 - Prob. 17ECh. 3.1 - Prob. 18ECh. 3.1 - Prob. 19ECh. 3.1 - Prob. 20ECh. 3.1 - Prob. 21ECh. 3.1 - Prob. 22ECh. 3.1 - Prob. 23ECh. 3.1 - Prob. 24ECh. 3.1 - Prob. 25ECh. 3.1 - Prob. 26ECh. 3.1 - Prob. 27ECh. 3.1 - Prob. 28ECh. 3.1 - Prob. 29ECh. 3.1 - Prob. 30ECh. 3.1 - In Exercises 31 and 32, complete the table by...Ch. 3.1 - In Exercises 31 and 32, complete the table by...Ch. 3.1 - Prob. 33ECh. 3.1 - Prob. 34ECh. 3.1 - In Exercises 33 through 40, determine the output...Ch. 3.1 - Prob. 36ECh. 3.1 - Prob. 37ECh. 3.1 - In Exercises 33 through 40, determine the output...Ch. 3.1 - Prob. 39ECh. 3.1 - In Exercises 33 through 40, determine the output...Ch. 3.1 - Prob. 41ECh. 3.1 - In Exercises 41 through 46, identify the...Ch. 3.1 - In Exercises 41 through 46, identify the...Ch. 3.1 - Prob. 44ECh. 3.1 - In Exercises 41 through 46, identify the errors....Ch. 3.1 - In Exercises 41 through 46, identify the...Ch. 3.1 - Prob. 47ECh. 3.1 - Prob. 48ECh. 3.1 - Prob. 49ECh. 3.1 - Prob. 50ECh. 3.1 - Prob. 51ECh. 3.1 - In Exercises 49 through 54, find the value of the...Ch. 3.1 - In Exercises 49 through 54, find the value of the...Ch. 3.1 - In Exercises 49 through 54, find the value of the...Ch. 3.1 - In Exercises 55 through 60, find the value of the...Ch. 3.1 - In Exercises 55 through 60, find the value of the...Ch. 3.1 - Prob. 57ECh. 3.1 - In Exercises 55 through 60, find the value of the...Ch. 3.1 - In Exercises 55 through 60, find the value of the...Ch. 3.1 - In Exercises 55 through 60, find the value of the...Ch. 3.1 - In Exercises 61 through 66, rewrite the statements...Ch. 3.1 - In Exercises 61 through 66, rewrite the statements...Ch. 3.1 - In Exercises 61 through 66, rewrite the statements...Ch. 3.1 - Prob. 64ECh. 3.1 - In Exercises 61 through 66, rewrite the statements...Ch. 3.1 - Prob. 66ECh. 3.1 - Prob. 67ECh. 3.1 - Prob. 68ECh. 3.1 - Prob. 69ECh. 3.1 - Prob. 70ECh. 3.1 - Prob. 71ECh. 3.1 - Prob. 72ECh. 3.1 - Prob. 73ECh. 3.1 - Prob. 74ECh. 3.1 - Prob. 75ECh. 3.1 - Prob. 76ECh. 3.1 - Prob. 77ECh. 3.1 - Prob. 78ECh. 3.1 - Prob. 79ECh. 3.1 - Prob. 80ECh. 3.1 - Prob. 81ECh. 3.1 - Prob. 82ECh. 3.1 - Prob. 83ECh. 3.1 - Prob. 84ECh. 3.1 - Prob. 85ECh. 3.1 - Prob. 86ECh. 3.2 - Prob. 1ECh. 3.2 - Prob. 2ECh. 3.2 - Prob. 3ECh. 3.2 - Prob. 4ECh. 3.2 - Prob. 5ECh. 3.2 - Prob. 6ECh. 3.2 - Prob. 7ECh. 3.2 - Prob. 8ECh. 3.2 - Prob. 9ECh. 3.2 - Prob. 10ECh. 3.2 - Prob. 11ECh. 3.2 - Prob. 12ECh. 3.2 - Prob. 13ECh. 3.2 - In Exercises 1 through 22, determine the output...Ch. 3.2 - Prob. 15ECh. 3.2 - Prob. 16ECh. 3.2 - Prob. 17ECh. 3.2 - Prob. 18ECh. 3.2 - Prob. 19ECh. 3.2 - Prob. 20ECh. 3.2 - Prob. 21ECh. 3.2 - In Exercises 1 through 22, determine the output...Ch. 3.2 - Prob. 23ECh. 3.2 - Prob. 24ECh. 3.2 - (True or False) If is the length of str, then is...Ch. 3.2 - (True or False) If n is the length of str, then ...Ch. 3.2 - Prob. 27ECh. 3.2 - Prob. 28ECh. 3.2 - Prob. 29ECh. 3.2 - Prob. 30ECh. 3.2 - Prob. 31ECh. 3.2 - Prob. 32ECh. 3.2 - Prob. 33ECh. 3.2 - In Exercises 27 through 34, identify any errors....Ch. 3.2 - Prob. 35ECh. 3.2 - Prob. 36ECh. 3.2 - Prob. 37ECh. 3.2 - Prob. 38ECh. 3.2 - Prob. 39ECh. 3.2 - Prob. 40ECh. 3.2 - Prob. 41ECh. 3.2 - In Exercises 39 through 44, write a program to...Ch. 3.2 - Prob. 43ECh. 3.2 - Prob. 44ECh. 3.2 - In the following exercises, write a program to...Ch. 3.2 - In the following exercises, write a program to...Ch. 3.2 - In the following exercises, write a program to...Ch. 3.2 - In the following exercises, write a program to...Ch. 3.2 - In the following exercises, write a program to...Ch. 3.2 - In the following exercises, write a program to...Ch. 3.2 - In the following exercises, write a program to...Ch. 3.2 - In the following exercises, write a program to...Ch. 3.2 - In the following exercises, write a program to...Ch. 3.2 - In the following exercises, write a program to...Ch. 3.2 - In the following exercises, write a program to...Ch. 3.2 - Prob. 56ECh. 3.2 - Prob. 57ECh. 3.2 - In the following exercises, write a program to...Ch. 3.2 - In the following exercises, write a program to...Ch. 3.2 - In the following exercises, write a program to...Ch. 3.2 - In the following exercises, write a program to...Ch. 3.2 - In the following exercises, write a program to...Ch. 3.3 - Prob. 1ECh. 3.3 - Prob. 2ECh. 3.3 - Prob. 3ECh. 3.3 - Prob. 4ECh. 3.3 - Prob. 5ECh. 3.3 - Prob. 6ECh. 3.3 - Prob. 7ECh. 3.3 - Prob. 8ECh. 3.3 - Prob. 9ECh. 3.3 - Prob. 10ECh. 3.3 - Prob. 11ECh. 3.3 - Prob. 12ECh. 3.3 - Prob. 13ECh. 3.3 - Prob. 14ECh. 3.3 - Prob. 15ECh. 3.3 - Prob. 16ECh. 3.3 - Prob. 17ECh. 3.3 - Prob. 18ECh. 3.3 - Prob. 19ECh. 3.3 - Prob. 20ECh. 3.3 - Prob. 21ECh. 3.3 - Prob. 22ECh. 3.3 - Prob. 23ECh. 3.3 - Prob. 24ECh. 3.3 - Prob. 25ECh. 3.3 - Prob. 26ECh. 3.3 - In Exercises 1 through 52, determine the output...Ch. 3.3 - Prob. 28ECh. 3.3 - Prob. 29ECh. 3.3 - Prob. 30ECh. 3.3 - Prob. 31ECh. 3.3 - Prob. 32ECh. 3.3 - Prob. 33ECh. 3.3 - Prob. 34ECh. 3.3 - Prob. 35ECh. 3.3 - Prob. 36ECh. 3.3 - Prob. 37ECh. 3.3 - Prob. 38ECh. 3.3 - In Exercises 1 through 52, determine the output...Ch. 3.3 - Prob. 40ECh. 3.3 - Prob. 41ECh. 3.3 - Prob. 42ECh. 3.3 - Prob. 43ECh. 3.3 - Prob. 44ECh. 3.3 - In Exercises 1 through 52, determine the output...Ch. 3.3 - Prob. 46ECh. 3.3 - Prob. 47ECh. 3.3 - Prob. 48ECh. 3.3 - In Exercises 1 through 52, determine the output...Ch. 3.3 - In Exercises 1 through 52, determine the output...Ch. 3.3 - Prob. 51ECh. 3.3 - Prob. 52ECh. 3.3 - In Exercises 53 through 56, determine the output...Ch. 3.3 - In Exercises 53 through 56, determine the output...Ch. 3.3 - Prob. 55ECh. 3.3 - In Exercises 53 through 56, determine the output...Ch. 3.3 - In Exercises 57 through 64, identify any errors....Ch. 3.3 - Prob. 58ECh. 3.3 - In Exercises 57 through 64, identify any...Ch. 3.3 - Prob. 60ECh. 3.3 - Prob. 61ECh. 3.3 - Prob. 62ECh. 3.3 - Prob. 63ECh. 3.3 - Prob. 64ECh. 3.3 - Prob. 65ECh. 3.3 - Prob. 66ECh. 3.3 - Prob. 67ECh. 3.3 - Prob. 68ECh. 3.3 - Prob. 69ECh. 3.3 - Prob. 70ECh. 3.3 - Prob. 71ECh. 3.3 - In Exercises 71 and 72, write a statement to carry...Ch. 3.3 - Prob. 73ECh. 3.3 - Prob. 74ECh. 3.3 - Prob. 75ECh. 3.3 - Prob. 76ECh. 3.3 - Prob. 77ECh. 3.3 - Prob. 78ECh. 3.3 - Prob. 79ECh. 3.3 - Prob. 80ECh. 3.3 - Prob. 81ECh. 3.3 - Prob. 82ECh. 3.3 - Prob. 83ECh. 3.3 - How Old Would You Be on Mercury? The length of a...Ch. 3.3 - Change in Salary A common misconception is that if...Ch. 3.3 - Prob. 86ECh. 3.3 - Prob. 87ECh. 3.3 - Marketing Terms The markup of an item is the...Ch. 3 - Calculator Write a program that allows the user to...Ch. 3 - Repair Bill Suppose automobile repair customers...Ch. 3 - Prob. 3PPCh. 3 - Length Conversion Write a program to convert a...Ch. 3 - Car Loan If A dollars are borrowed at r interest...Ch. 3 - Prob. 6PPCh. 3 - Bond Yield One measure of a bond's performance is...
Additional Engineering Textbook Solutions
Find more solutions based on key concepts
What is a property?
Starting Out With Visual Basic (8th Edition)
Repeat Programming Project 8 in Chapter 1, but add yes-or-no dialogs to allow the user to make the following co...
Java: An Introduction to Problem Solving and Programming (8th Edition)
Functions make it easier for programmers to work in teams.
Starting Out with Python (4th Edition)
Land Calculation One acre of land is equivalent to 43,560 square feet. Design a program that asks the user to e...
Starting Out with Programming Logic and Design (5th Edition) (What's New in Computer Science)
This optional Google account security feature sends you a message with a code that you must enter, in addition ...
SURVEY OF OPERATING SYSTEMS
isMember Method Write a recursive boolean method named isMember. The method should search an array for a specif...
Starting Out with Java: From Control Structures through Data Structures (4th Edition) (What's New in Computer Science)
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Solve this "Do not use AI tools. Solve the problem by hand on paper only and upload a photo of your handwritten solution."arrow_forwardSolve this "Do not use AI tools. Solve the problem by hand on paper only and upload a photo of your handwritten solution."arrow_forwardSolve this "Do not use AI tools. Solve the problem by hand on paper only and upload a photo of your handwritten solution."arrow_forward
- Solve this "Do not use AI tools. Solve the problem by hand on paper only and upload a photo of your handwritten solution."arrow_forwardSolve this "Do not use AI tools. Solve the problem by hand on paper only and upload a photo of your handwritten solution."arrow_forwardSolve this "Do not use AI tools. Solve the problem by hand on paper only and upload a photo of your handwritten solution."arrow_forward
- In three years, assuming the competitive environment remains unchanged, how many units of Bat will Baldwin be selling in the Nano market segment? a) 639 b) 561 c) 431 d) 716arrow_forwardBrand managers know that increasing promotional budgets eventually result in diminishing returns. The first one million dollars typically results in a 26% increase in awareness, while the second million results in adding another 18% and the third million in a 5% increase. Andrews’s product Alan currently has an awareness level of 80% . While an important product for Andrews, Alan’s promotion budget will be reduced to one million dollars for the upcoming year. Assuming that Alan loses one-third of its awareness each year, what will Alan’s awareness level be next year? a) 79% b) 53% c) 74% d) 58%arrow_forwardDo not use A.I and solve completelyarrow_forward
- Solve thisarrow_forwardSpecifications: Part-1Part-1: DescriptionIn this part of the lab you will build a single operation ALU. This ALU will implement a bitwise left rotation. Forthis lab assignment you are not allowed to use Digital's Arithmetic components.IF YOU ARE FOUND USING THEM, YOU WILL RECEIVE A ZERO FOR LAB2!The ALU you will be implementing consists of two 4-bit inputs (named inA and inB) and one 4-bit output (named out). Your ALU must rotate the bits in inA by the amount given by inB (i.e. 0-15).Part-1: User InterfaceYou are provided an interface file lab2_part1.dig; start Part-1 from this file.NOTE: You are not permitted to edit the content inside the dotted lines rectangle.Part-1: ExampleIn the figure above, the input values that we have selected to test are inA = {inA_3, inA_2, inA_1, inA_0} = {0, 1, 0,0} and inB = {inB_3, inB_2, inB_1, inB_0} = {0, 0, 1, 0}. Therefore, we must rotate the bus 0100 bitwise left by00102, or 2 in base 10, to get {0, 0, 0, 1}. Please note that a rotation left is…arrow_forwardHow can I perform Laplace Transformation when using integration based on this? Where we convert time-based domain to frequency domainarrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage Learning
C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage Learning C++ for Engineers and ScientistsComputer ScienceISBN:9781133187844Author:Bronson, Gary J.Publisher:Course Technology PtrProgramming Logic & Design ComprehensiveComputer ScienceISBN:9781337669405Author:FARRELLPublisher:Cengage
C++ for Engineers and ScientistsComputer ScienceISBN:9781133187844Author:Bronson, Gary J.Publisher:Course Technology PtrProgramming Logic & Design ComprehensiveComputer ScienceISBN:9781337669405Author:FARRELLPublisher:Cengage- Np Ms Office 365/Excel 2016 I NtermedComputer ScienceISBN:9781337508841Author:CareyPublisher:Cengage
 EBK JAVA PROGRAMMINGComputer ScienceISBN:9781337671385Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT
EBK JAVA PROGRAMMINGComputer ScienceISBN:9781337671385Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT

C++ Programming: From Problem Analysis to Program...
Computer Science
ISBN:9781337102087
Author:D. S. Malik
Publisher:Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Course Technology Ptr

Programming Logic & Design Comprehensive
Computer Science
ISBN:9781337669405
Author:FARRELL
Publisher:Cengage

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:9781337508841
Author:Carey
Publisher:Cengage

EBK JAVA PROGRAMMING
Computer Science
ISBN:9781337671385
Author:FARRELL
Publisher:CENGAGE LEARNING - CONSIGNMENT
Boolean Algebra - Digital Logic and Logic Families - Industrial Electronics; Author: Ekeeda;https://www.youtube.com/watch?v=u7XnJos-_Hs;License: Standard YouTube License, CC-BY
Boolean Algebra 1 – The Laws of Boolean Algebra; Author: Computer Science;https://www.youtube.com/watch?v=EPJf4owqwdA;License: Standard Youtube License