Big Java Late Objects
2nd Edition
ISBN: 9781119330455
Author: Horstmann
Publisher: WILEY
expand_more
expand_more
format_list_bulleted
Concept explainers
Textbook Question
Chapter 5.5, Problem 16SC
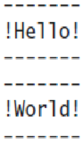
How do you generate the following printout, using the boxString method?
Expert Solution & Answer
Want to see the full answer?
Check out a sample textbook solution
Students have asked these similar questions
Specifications: Part-1Part-1: DescriptionIn this part of the lab you will build a single operation ALU. This ALU will implement a bitwise left rotation. Forthis lab assignment you are not allowed to use Digital's Arithmetic components.IF YOU ARE FOUND USING THEM, YOU WILL RECEIVE A ZERO FOR LAB2!The ALU you will be implementing consists of two 4-bit inputs (named inA and inB) and one 4-bit output (named
out). Your ALU must rotate the bits in inA by the amount given by inB (i.e. 0-15).Part-1: User InterfaceYou are provided an interface file lab2_part1.dig; start Part-1 from this file.NOTE: You are not permitted to edit the content inside the dotted lines rectangle.Part-1: ExampleIn the figure above, the input values that we have selected to test are inA = {inA_3, inA_2, inA_1, inA_0} = {0, 1, 0,0} and inB = {inB_3, inB_2, inB_1, inB_0} = {0, 0, 1, 0}. Therefore, we must rotate the bus 0100 bitwise left by00102, or 2 in base 10, to get {0, 0, 0, 1}. Please note that a rotation left is…
How can I perform Laplace Transformation when using integration based on this? Where we convert time-based domain to frequency domain
what would be the best way I can explain the bevhoirs of Laplace and Inverse Transofrmation In MATLAB.
Chapter 5 Solutions
Big Java Late Objects
Ch. 5.1 - Consider the method call Math.pow(3, 2). What are...Ch. 5.1 - What is the return value of the method call...Ch. 5.1 - The Math.ceil method in the Java standard library...Ch. 5.1 - It is possible to determine the answer to Self...Ch. 5.2 - What is the value of cubeVolume(3)?Ch. 5.2 - Prob. 6SCCh. 5.2 - Provide an alternate implementation of the body of...Ch. 5.2 - Declare a method squareArea that computes the area...Ch. 5.2 - Consider this method: public static int...Ch. 5.3 - What does this program print? Use a diagram like...
Ch. 5.3 - Prob. 11SCCh. 5.3 - What does this program print? Use a diagram like...Ch. 5.4 - Prob. 13SCCh. 5.4 - What does this method do? public static boolean...Ch. 5.4 - Implement the mystery method of Self Check 14 with...Ch. 5.5 - How do you generate the following printout, using...Ch. 5.5 - Prob. 17SCCh. 5.5 - Prob. 18SCCh. 5.5 - Prob. 19SCCh. 5.5 - The boxString method contains the code for...Ch. 5.6 - Consider the following statements: int...Ch. 5.6 - Consider this method that prints a page number on...Ch. 5.6 - Consider the following method that computes...Ch. 5.6 - The comment explains what the following loop does....Ch. 5.6 - In Self Check 24, you were asked to implement a...Ch. 5.7 - Explain how you can improve the intName method so...Ch. 5.7 - Prob. 27SCCh. 5.7 - What happens when you call intName(0)? How can you...Ch. 5.7 - Trace the method call intName(72), as described in...Ch. 5.7 - Prob. 30SCCh. 5.8 - Which lines are in the scope of the variable i...Ch. 5.8 - Which lines are in the scope of the parameter...Ch. 5.8 - The program declares two local variables with the...Ch. 5.8 - There is a scope error in the mystery method. How...Ch. 5.8 - Prob. 35SCCh. 5.9 - Consider this slight modification of the...Ch. 5.9 - Consider this recursive method: public static int...Ch. 5.9 - Consider this recursive method: public static int...Ch. 5.9 - Prob. 39SCCh. 5.9 - The intName method in Section 5.7 accepted...Ch. 5 - In which sequence are the lines of the Cubes.java...Ch. 5 - Write method headers for methods with the...Ch. 5 - Give examples of the following methods from the...Ch. 5 - Prob. 4RECh. 5 - Consider these methods: public static double...Ch. 5 - Prob. 6RECh. 5 - Design a method that prints a floating-point...Ch. 5 - Write pseudocode for a method that translates a...Ch. 5 - Describe the scope error in the following program...Ch. 5 - For each of the variables in the following...Ch. 5 - Prob. 11RECh. 5 - Perform a walkthrough of the intName method with...Ch. 5 - Consider the following method: public static int...Ch. 5 - Consider the following method that is intended to...Ch. 5 - Suppose an ancient civilization had constructed...Ch. 5 - Give pseudocode for a recursive method for...Ch. 5 - Give pseudocode for a recursive method that sorts...Ch. 5 - Write the following methods and provide a program...Ch. 5 - Write the following methods and provide a program...Ch. 5 - Prob. 4PECh. 5 - Prob. 5PECh. 5 - Prob. 6PECh. 5 - Prob. 7PECh. 5 - Prob. 8PECh. 5 - Write methods public static double...Ch. 5 - Write a recursive method public static String...Ch. 5 - Write a recursive method public static boolean...Ch. 5 - Use recursion to implement a method public static...Ch. 5 - Use recursion to determine the number of digits in...Ch. 5 - Write a method that computes the balance of a bank...Ch. 5 - Write a method that tests whether a file name...Ch. 5 - It is a well-known phenomenon that most people are...Ch. 5 - Prob. 3PPCh. 5 - Use recursion to compute an, where n is a positive...Ch. 5 - Leap years. Write a method public static boolean...Ch. 5 - In Exercise P3.13 you were asked to write a...Ch. 5 - Prob. 10PPCh. 5 - Write a program that reads two strings containing...Ch. 5 - Prob. 12PPCh. 5 - Write a program that reads words and arranges them...Ch. 5 - Prob. 14PPCh. 5 - Write a program that reads two fractions, adds...Ch. 5 - Write a program that prints the decimal expansion...Ch. 5 - Write a program that reads a decimal expansion...Ch. 5 - Write two methods public static void...Ch. 5 - Write a program that reads in the width and height...Ch. 5 - Repeat Exercise P5.19 with hexagonal circle...Ch. 5 - Postal bar codes. For faster sorting of letters,...Ch. 5 - Write a program that reads in a bar code (with :...Ch. 5 - Write a program that converts a Roman number such...Ch. 5 - A non-governmental organization needs a program to...Ch. 5 - Having a secure password is a very important...Ch. 5 - Prob. 30PPCh. 5 - Prob. 31PPCh. 5 - Electric wire, like that in the photo, is a...Ch. 5 - The drag force on a car is given by FD=12v2ACD...
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- What IETF protocol is NetFlow associated with? Group of answer choices IPX/SPX IPIX HTTPS SSHarrow_forwardHow can I perform Laplace Transformation when using integration based on this?arrow_forwardWrite an example of a personal reflection of your course. - What you liked about the course. - What you didn’t like about the course. - Suggestions for improvement. Course: Information and Decision Sciences (IDS) The Reflection Paper should be 1 or 2 pages in length.arrow_forward
- using r languagearrow_forwardI need help in explaining how I can demonstrate how the Laplace & Inverse transformations behaves in MATLAB transformation (ex: LIke in graph or something else)arrow_forwardYou have made the Web solution with Node.js. please let me know what problems and benefits I would experience while making the Web solution here, as compared to any other Web solution you have developed in the past. what problems and benefits/things to keep in mind as someone just learningarrow_forward
- PHP is the server-side scripting language. MySQL is used with PHP to store all the data. EXPLAIN in details how to install and run the PHP/MySQL on your computer. List the issues and challenges I may encounter while making this set-up? why I asked: I currently have issues logging into http://localhost/phpmyadmin/ and I tried using the command prompt in administrator to reset the password but I got the error LOCALHOST PORT not found.arrow_forwardHTML defines content, CSS defines layout, and JavaScript adds logic to the website on the client side. EXPLAIN IN DETAIL USING an example.arrow_forwardusing r languangearrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage LearningNp Ms Office 365/Excel 2016 I NtermedComputer ScienceISBN:9781337508841Author:CareyPublisher:Cengage
C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage LearningNp Ms Office 365/Excel 2016 I NtermedComputer ScienceISBN:9781337508841Author:CareyPublisher:Cengage EBK JAVA PROGRAMMINGComputer ScienceISBN:9781337671385Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT
EBK JAVA PROGRAMMINGComputer ScienceISBN:9781337671385Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT New Perspectives on HTML5, CSS3, and JavaScriptComputer ScienceISBN:9781305503922Author:Patrick M. CareyPublisher:Cengage Learning
New Perspectives on HTML5, CSS3, and JavaScriptComputer ScienceISBN:9781305503922Author:Patrick M. CareyPublisher:Cengage Learning Microsoft Visual C#Computer ScienceISBN:9781337102100Author:Joyce, Farrell.Publisher:Cengage Learning,
Microsoft Visual C#Computer ScienceISBN:9781337102100Author:Joyce, Farrell.Publisher:Cengage Learning,

C++ Programming: From Problem Analysis to Program...
Computer Science
ISBN:9781337102087
Author:D. S. Malik
Publisher:Cengage Learning

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:9781337508841
Author:Carey
Publisher:Cengage

EBK JAVA PROGRAMMING
Computer Science
ISBN:9781337671385
Author:FARRELL
Publisher:CENGAGE LEARNING - CONSIGNMENT


New Perspectives on HTML5, CSS3, and JavaScript
Computer Science
ISBN:9781305503922
Author:Patrick M. Carey
Publisher:Cengage Learning

Microsoft Visual C#
Computer Science
ISBN:9781337102100
Author:Joyce, Farrell.
Publisher:Cengage Learning,
9.1: What is an Array? - Processing Tutorial; Author: The Coding Train;https://www.youtube.com/watch?v=NptnmWvkbTw;License: Standard Youtube License