Concept explainers
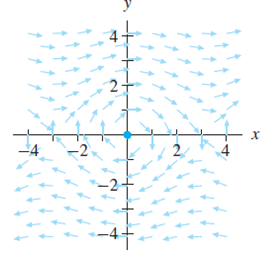
In Exercises 3—6, a system, an initial condition, a step size, and an integer n are given. The direction field for the system is also provided.
(a) Use EulersMethodForSystems to calculate the approximate solution given by Euler’s method for the given system with the given initial condition and step size for n steps.
(b) Plot your approximate solution on the direction field. Make sure that your approximate solution is consistent with the direction field.
(c) Using HPGSystemSolver, obtain a more detailed sketch of the phase portrait for the system.
5.
Want to see the full answer?
Check out a sample textbook solution
Chapter 2 Solutions
DIFFERENTIAL EQUATIONS-ACCESS
- Show all workarrow_forwardQ4: Discuss the stability critical point of the ODES x + sin(x) = 0 and draw phase portrait.arrow_forwardUsing Karnaugh maps and Gray coding, reduce the following circuit represented as a table and write the final circuit in simplest form (first in terms of number of gates then in terms of fan-in of those gates). HINT: Pay closeattention to both the 1’s and the 0’s of the function.arrow_forward
- Recall the RSA encryption/decryption system. The following questions are based on RSA. Suppose n (=15) is the product of the two prime numbers 3 and 5.1. Find an encryption key e for for the pair (e, n)2. Find a decryption key d for for the pair (d, n)3. Given the plaintext message x = 3, find the ciphertext y = x^(e) (where x^e is the message x encoded with encryption key e)4. Given the ciphertext message y (which you found in previous part), Show that the original message x = 3 can be recovered using (d, n)arrow_forwardTheorem 1: A number n ∈ N is divisible by 3 if and only if when n is writtenin base 10 the sum of its digits is divisible by 3. As an example, 132 is divisible by 3 and 1 + 3 + 2 is divisible by 3.1. Prove Theorem 1 2. Using Theorem 1 construct an NFA over the alphabet Σ = {0, 1, 2, 3, 4, 5, 6, 7, 8, 9}which recognizes the language {w ∈ Σ^(∗)| w = 3k, k ∈ N}.arrow_forwardRecall the RSA encryption/decryption system. The following questions are based on RSA. Suppose n (=15) is the product of the two prime numbers 3 and 5.1. Find an encryption key e for for the pair (e, n)2. Find a decryption key d for for the pair (d, n)3. Given the plaintext message x = 3, find the ciphertext y = x^(e) (where x^e is the message x encoded with encryption key e)4. Given the ciphertext message y (which you found in previous part), Show that the original message x = 3 can be recovered using (d, n)arrow_forward
- Find the sum of products expansion of the function F(x, y, z) = ¯x · y + x · z in two ways: (i) using a table; and (ii) using Boolean identities.arrow_forwardGive both a machine-level description (i.e., step-by-step description in words) and a state-diagram for a Turing machine that accepts all words over the alphabet {a, b} where the number of a’s is greater than or equal to the number of b’s.arrow_forwardCompute (7^ (25)) mod 11 via the algorithm for modular exponentiation.arrow_forward
- Algebra & Trigonometry with Analytic GeometryAlgebraISBN:9781133382119Author:SwokowskiPublisher:Cengage
 Linear Algebra: A Modern IntroductionAlgebraISBN:9781285463247Author:David PoolePublisher:Cengage Learning
Linear Algebra: A Modern IntroductionAlgebraISBN:9781285463247Author:David PoolePublisher:Cengage Learning

