
Concept explainers
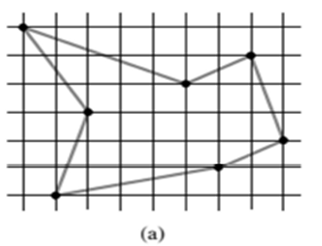
(a)
To describe a dynamic-
(a)
Explanation of Solution
Given Information:
The shortest closed tour of the graph with length approximately is 24.89. The directed acyclic graph is shown below-
Explanation:
The dynamic-approach used to find the longest length simple path consider the graph G and vertices as V. The longest simple path must go through some edge of weight s or t . The algorithms to compute the longest weight path is
The base condition for the algorithm is
The algorithm to compute longest simple path in a directed acyclic graph is given below-
LONG-PATH(G,u,s,t,len)
If
set
return ( len,u )
else if
Return (len,u).
else
for each adjacent vertex
Check the distance after adding new vertex i.
if
end if.
end for.
end if.
return ( len,u ).
end.
In above algorithm, loop of for is used to determine the longest path and the longest path visit all vertex by checking all adjacent vertex.
The time taken by the algorithm is depends upon the number of vertex visited and the number of edges in the longest simple path. Suppose V represent the number of vertex used in the computing the longest simple path and E represent the number of edges then total running time of the algorithm is equals to
(b)
To describe a dynamic-programming approach for finding longest simple path in directed acyclic graph and also give the running time of the algorithm.
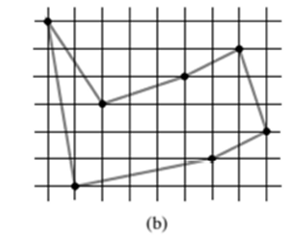
(b)
Explanation of Solution
Given Information:
The shortest closed tour of the graph with length approximately is 25.58. The directed acyclic graph is shown below-
Explanation:
The longest simple path must go through some edge of weight s . The base condition for the algorithm is
The algorithm to compute longest simple path in a directed acyclic graph is given below-
LONG-PATH(G,u,s,t,len)
If
set
return ( len,u )
else if
Return (len,u).
else
for each adjacent vertex
Check the distance after adding new vertex i.
if
end if.
end for.
end if.
return ( len,u ).
end.
The time taken by the algorithm is depends upon the number of vertex visited and the number of edges in the longest simple path. Suppose V represent the number of vertex used in the computing the longest simple path and E represent the number of edges then total running time of the algorithm is equals to
The above algorithm taken consideration of the nodes and generates the output according to the number of nodes in the graph so the longest length is computed by
Want to see more full solutions like this?
Chapter 15 Solutions
Introduction to Algorithms
- I need help in explaining how I can demonstrate how the Laplace & Inverse transformations behaves in MATLAB transformation (ex: LIke in graph or something else)arrow_forwardYou have made the Web solution with Node.js. please let me know what problems and benefits I would experience while making the Web solution here, as compared to any other Web solution you have developed in the past. what problems and benefits/things to keep in mind as someone just learningarrow_forwardPHP is the server-side scripting language. MySQL is used with PHP to store all the data. EXPLAIN in details how to install and run the PHP/MySQL on your computer. List the issues and challenges I may encounter while making this set-up? why I asked: I currently have issues logging into http://localhost/phpmyadmin/ and I tried using the command prompt in administrator to reset the password but I got the error LOCALHOST PORT not found.arrow_forward
 Operations Research : Applications and AlgorithmsComputer ScienceISBN:9780534380588Author:Wayne L. WinstonPublisher:Brooks Cole
Operations Research : Applications and AlgorithmsComputer ScienceISBN:9780534380588Author:Wayne L. WinstonPublisher:Brooks Cole Fundamentals of Information SystemsComputer ScienceISBN:9781305082168Author:Ralph Stair, George ReynoldsPublisher:Cengage Learning
Fundamentals of Information SystemsComputer ScienceISBN:9781305082168Author:Ralph Stair, George ReynoldsPublisher:Cengage Learning C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage Learning
C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage Learning Principles of Information Systems (MindTap Course...Computer ScienceISBN:9781285867168Author:Ralph Stair, George ReynoldsPublisher:Cengage LearningNp Ms Office 365/Excel 2016 I NtermedComputer ScienceISBN:9781337508841Author:CareyPublisher:Cengage
Principles of Information Systems (MindTap Course...Computer ScienceISBN:9781285867168Author:Ralph Stair, George ReynoldsPublisher:Cengage LearningNp Ms Office 365/Excel 2016 I NtermedComputer ScienceISBN:9781337508841Author:CareyPublisher:Cengage





