(Variable-Length Argument List: Calculating Products) Write a
Program Plan:
This header file <stdarg.h>is used for object ap of type va_list is used by macros va_startva_arg and va_end to process the variable-length argument list of function product.
product( int x, ) :This function definition product is using a variable length argument list and calculate the product of a series of integers.
Printf (): used to print the data onto output screen.
Variables i, j, l, m, and n are of integer type which are passed as argument to function.
Total variable of integer type is used to store product of integer value.
Program Description: Purpose of the program is to calculates the series of integers that are passed to function product with several calls, by using a variable length list of arguments list and display result.
Explanation of Solution
Program: Following is Cprogram that calculates the series of integers that are passed to function product with several calls, by using a variable length list of arguments list and display result.
#include<stdio.h>//header file
#include<stdarg.h>///header-file for variable-length argument lists
//Function prototype
int product( int x, ... );
//Start of main
intmain( void )
{
//Initialize the integers
inti = 5;
int j = 4;
int k = 3;
int l = 2;
int m = 1;
//display user the values of integers
printf( "%s%d\n%s%d\n%s%d\n%s%d\n%s%d\n","i = ",
i, "j = ", j,"k = ", k,"l = ", l, "m = ", m );
//display the result of product using the function call to different series of integers
printf( "%s%d\n%s%d\n%s%d\n%s%d\n",
"The Product of i and j is: ", product( 2,i,j ),
"The Product of i, j and k is: ",product(3,i,j,k ),
"The Product of i, j, k and 1 is: ", product(4,i,j,k,l ),
"The Product of i, j, k, 1, and m is: ",product(5,i,j,k,l,m) );
//terminate program succesfully
return0;
}//End of main
//function product in which product of integers is passed as arguments
int product( int x, ... )
{
//Declare and initialize variable total
int total = 1;
//variable to counter loop
intz;
//Stores information needed by va_start and va_end.
/*initialize variable Length argument List*/
va_listarg;
//Stores information needed by va_start.
/*invoke the macros to access the arguments*/
va_start( arg, x );
//Process is running for variable length argument list.
/*evaluate the total using for loop*/
for( z = 1; z <= x ; z++ )
{
total *= va_arg( arg, int);
}/*end of for loop*/
//Clean up variable-length argument list.
/*Perform the housekeeping termination*/
va_end( arg);
/*return the arguments of product*/
returntotal;
}/*end of function Product*/
Explanation:
- Use header file notation
for variable-length list of arguments. - Read different series of integers in function call.
- Assign the value of total equals to 1 and use the argument list including va_list of variable list, next initialize va_start ( ) to invoke the macros so as to access the arguments in function definition.
- Loop for to evaluate the value of product.
- Display the product of a series of integers.
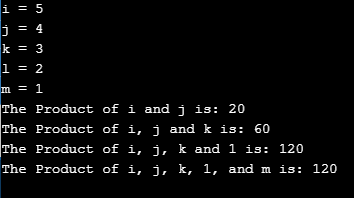
Sample Output:
Want to see more full solutions like this?
Chapter 14 Solutions
C How to Program (8th Edition)
Additional Engineering Textbook Solutions
Modern Database Management
Management Information Systems: Managing The Digital Firm (16th Edition)
SURVEY OF OPERATING SYSTEMS
Starting Out with Java: From Control Structures through Data Structures (4th Edition) (What's New in Computer Science)
Java How to Program, Early Objects (11th Edition) (Deitel: How to Program)
Starting Out with C++ from Control Structures to Objects (9th Edition)
 C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage Learning
C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage Learning C++ for Engineers and ScientistsComputer ScienceISBN:9781133187844Author:Bronson, Gary J.Publisher:Course Technology Ptr
C++ for Engineers and ScientistsComputer ScienceISBN:9781133187844Author:Bronson, Gary J.Publisher:Course Technology Ptr Microsoft Visual C#Computer ScienceISBN:9781337102100Author:Joyce, Farrell.Publisher:Cengage Learning,
Microsoft Visual C#Computer ScienceISBN:9781337102100Author:Joyce, Farrell.Publisher:Cengage Learning,


