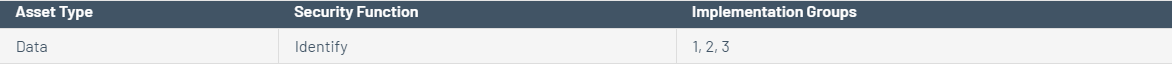
CIS Control 13: Data Protection Asset Sub- Control Type 13.1 Data Security Function Identify Control Title Maintain an Inventory of Sensitive Information Control Descriptions Maintain an inventory of all sensitive information stored, processed, or transmitted by the organization's technology systems, including those located on-site or at a remote service provider. Implementation Groups 1 2 3

Check CIS 13: Data protection
The aim of this control is to ensure that all data is classified and protected in accordance with established data classifications. To create these data classifications, organizations should create a list of key data types and define the overall importance to the organization. This can be used to create a data classification scheme for an organization. Labels such as "Sensitive", "Commercially Confidential" and "Public" should be used. Information owners must be aware of the classification policy and tools, procedures and controls of said data.
13.1: Maintain an Inventory of Sensitive Information
Tenable.sc supports an MDM integration solution, but the purpose is to detect vulnerabilities on mobile devices. Details of data stored on mobile devices are not recorded in the data received from the MDM solution. Any MDM solution that an organization uses should support the requirement to enable encryption.
Step by step
Solved in 2 steps with 2 images









